Digital data has become the lifeblood of every enterprise, and data loss prevention (DLP) is no longer optional. Among leading solutions, Forcepoint DLP and AnySecura DLP stand out with years of industry experience. But which one is truly the right fit for your business?
This article compares Forcepoint DLP vs AnySecura across core features, deployment flexibility, and enterprise use cases—helping you make a confident decision.
👉You may also want to know: AnySecura vs Teramind: Employee Monitoring Tool Comparison (2026).

What are Forcepoint DLP and AnySecura?
What is Forcepoint DLP?
Forcepoint DLP centers on business compliance, with a core focus on shielding sensitive data from leaks across channels like email, web, SaaS platforms, endpoints, IaaS / PaaS, Cloud servers, and AI systems.
What is AnySecura?
AnySecura specializes in comprehensive enterprise management and data protection, standing out for monitoring risky activities, controlling access across applications and devices, and logging key operations to support compliance and post-incident audits.
The Core Differences: Forcepoint DLP vs AnySecura
The Key Features of Forcepoint DLP
Forcepoint's monitoring and control capabilities are particularly remarkable when data flows through specific and well-defined channels. For enterprises that are highly concerned about data leakage, its modular product architecture offers numerous advantages, primarily focusing on two core scenarios.
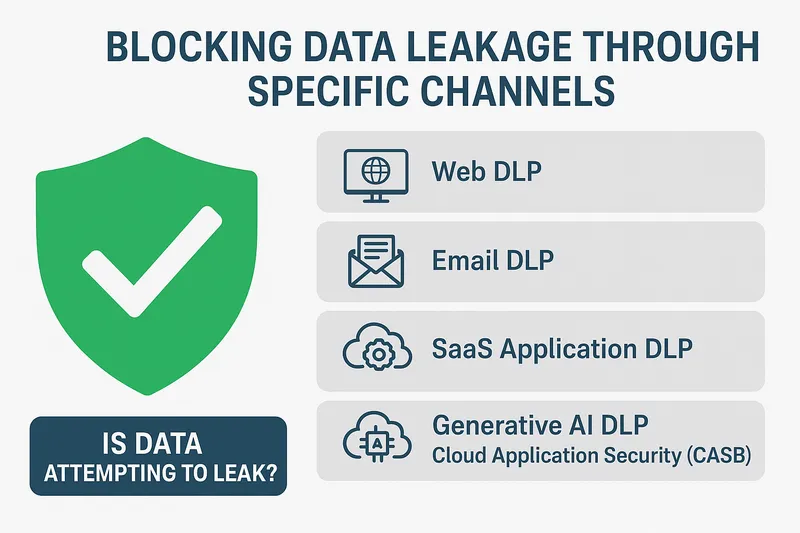
In terms of digital communication channels, Forcepoint excels with its web DLP, email DLP, and SaaS application DLP solutions, enabling precise control over data transmission through these channels. To address current cloud and AI threats, Forcepoint has specifically adapted to these new trends by deploying generative AI DLP and Cloud Application Security (CASB) capabilities, effectively protecting data on platforms such as ChatGPT, Salesforce, and AWS.
Ultimately, Forcepoint's protection strategy revolves around a central question: "Is data attempting to leak through monitored channels?"
The Key Features of AnySecura
Unlike Forcepoint, AnySecura adopts a more comprehensive and in-depth protection approach at its core. It is well aware that data risks are not limited to the transmission stage. Risks of leakage during static storage, operational risks during dynamic use, and even accidental misoperations of various devices within the corporate intranet by personnel can all pose threats to data security. As evidenced by its extensive list of modules, AnySecura aims to address a broader range of issues:
- 1. What exactly is data?
- 2. Where is the data stored?
- 3. How is the data being used?
- 4. Who is using the data? On what devices?
- 5. How can we prevent misuse before it happens?
- 6. How can we secure it intrinsically?
In short, AnySecura's protection logic focuses on a set of core questions: "What is data? Where is it stored? Who uses it? And how can we protect its security at every point of contact?"

Discover how DLP software delivers compliance, prevents insider threats, and secures sensitive information across endpoints, cloud services, and networks. Learn more>>
Key Features Comparison: AnySecura DLP vs Forcepoint DLP
| Aspect | AnySecura DLP | Forcepoint DLP |
|---|---|---|
| Scope of Protection | It takes into account both the data itself and its distribution channels. Whether it is static data in storage, data in use, or dynamic data flowing between terminals, networks, and applications, it can be covered. | Pay attention to the channels through which data leaks occur. Focus on data flowing through major channels like web pages, email, and the cloud, often referred to as "data in motion." |
| Endpoint & Human Focus | It can provide in-depth terminal control and complete chain auditing. It includes functions such as device control, print control, screen monitoring, and AI visual perception, which can monitor user operations in real time. | The ability to associate with terminals is relatively limited, and most of the time it is only used for DLP scanning. |
| Operational Integration | It can connect IT and security. It integrates IT asset management and remote maintenance functions, helping security teams and IT operations teams eliminate collaboration barriers. | It is mainly a security and compliance tool, relatively independent in function, and has little connection with other business links. |
| Proactive & Auditing Tools | Advanced forensic capabilities, such as watermarking and traceability, can deter leaks and track data flows. Security audit reports are also available to meet comprehensive compliance inspection needs. | Most of the alerts are for policy violations in the channels they cover, and their forms are relatively simple. |
| Deployment & Cost | It is a modular design, which can be purchased according to needs and can be combined arbitrarily, which is flexible. | It is a unified platform architecture. All functions are integrated together. |
Forcepoint DLP Modules vs AnySecura DLP Modules
The bottom line, Forcepoint DLP acts as a robust safety net, designed to catch and prevent sensitive data leaks before they occur. AnySecura, by contrast, goes beyond basic protection—it ensures tight oversight of all data-related channels through specialized modules, merging security with actionable management. Let's outline the differences in a comparison table, with a clear display of the modules provided by each one.
* The highlighted text below indicates that the module has overlapping functions, though they are not identical.
* The module comparison data is derived directly from the latest information available on AnySecura's and Forcepoint DLP's official websites.
| AnySecura DLP Modules | Forcepoint DLP Modules |
|---|---|
|
|
Forcepoint DLP Modules
Forcepoint DLP includes 8 modules to comprehensively protect sensitive data from leakage across all channels, from endpoints such as devices, USBs, printers, to cloud servers.
1. Endpoint DLP
Provide comprehensive security protection for enterprise endpoints and personal devices (BYOD). It's the last line of defense against data breaches. Deploy a lightweight protection agent on endpoints to strictly enforce security policies, regardless of whether the device is connected to the corporate network. Control unauthorized operations such as USB copying and confidential printing, physically blocking data leaks. Protection policies persist even when the device is offline. 24/7 data security is protected, eliminating any loopholes for risk.
2. Web DLP
Build a secure web gateway to manage network interactions. It protects against data risks and threats on the web. As a unified security control point for web traffic, it responds promptly. It blocks malicious websites, preventing malware from being downloaded from the web to devices. It also monitors data uploads to prevent unauthorized data from flowing to non-compliant locations.
3. Email DLP
Build a comprehensive email protection system. It must block both inbound threats and outbound data leaks. Scan emails before they reach the inbox. Filter out malware and phishing attempts. Check employee outgoing emails as well. If they contain sensitive information, handle them according to pre-set policies. Either block them or encrypt them. Transform email into a controllable and secure channel. Provide audit support to the CISO and ensure compliance.
4. SaaS Apps DLP
Rely on the Cloud Access Security Broker (CASB) architecture. Its core mission is to protect data within SaaS applications, enabling enterprises to safely use cloud productivity tools. The protection scope is broad, encompassing both mainstream SaaS suites and niche cloud tools. No security blind spots are left. Cloud application usage can be directly visualized, and unauthorized cloud services can be managed. Security policies can be enforced directly within SaaS applications, quickly ensuring that unauthorized application use and excessive sharing of confidential files can be promptly restricted.
5. Cloud App Security (CASB)
Managing sensitive information in the cloud is key. Enterprises must maintain control over cloud data. Continuously audit the configuration of IaaS/PaaS resources without compromising on performance. Immediately alert users of misconfigured storage buckets, such as public ones. Use anomaly detection to identify suspicious access patterns. For example, access from an unseen geographic location should be a cause for concern. A centralized management platform is convenient. In a multi-cloud environment, data visibility across platforms is maintained, allowing for unified management and control.
6. Custom App DLP
Embed data security capabilities into the company's customized applications. This eliminates security vulnerabilities in specific scenarios and addresses protection shortcomings. Provide uncomplicated integration solutions such as APIs and SDKs. Integrate data classification and data leakage prevention capabilities into the company's own or industry-specific customized applications. Use centralized policy management and unified standards. Regardless of the diversity of customized application architectures, they must adhere to the same security standards. A compliance verification framework is also available to audit customized code. This reassures the company's Chief Information Security Officer (CISO) that customized applications fully comply with data protection requirements.
7. IaaS/PaaS DLP
Provide hybrid protection for local and cloud servers. The goal is clear: to ensure data security on IaaS/PaaS platforms while also providing management and control capabilities. Automatically locate sensitive data in cloud storage, such as S3, Blob Storage, and databases. Once found, maintain control and continuously monitor the status of this data. React quickly to any abnormal access or configuration issues. High-risk issues are flagged in real time and blocked immediately to prevent cloud data leaks.
8. Generative AI DLP
It scans in real time and immediately blocks any sensitive information sent by employees to AI without hesitation. This allows businesses to customize their policies based on their needs, offering a high degree of flexibility. Complying with regulations like GDPR and HIPAA is crucial, and there are two benefits to this approach: first, it alleviates management concerns about AI data leaks; second, it allows employees to use AI with confidence while ensuring normal work needs.
AnySecura DLP Modules
AnySecura's core focus is on flexible, enterprise-grade data loss prevention solutions, allowing users to choose from over 20 modules based on their business needs. Through different combinations, they can perfectly meet the data protection needs of different companies.

Document Control
Document Control module can record logs of all document operations, burning, and ADB transmissions, and can also manage document read, write, and delete permissions, helping enterprises to make document operations traceable and prevent violations. In addition, it has a document backup function and supports copying documents to a network disk through application or filing, which not only solves the problem of accidental deletion and tampering of documents that enterprises are worried about, but also does not affect daily business operations.
Print Control
Print Control module records detailed information about all printing operations, including the time, user, and printer. It also backs up printed content and controls printing permissions, allowing businesses to review printing records at any time and prevent illegal printing. It supports customizable print watermarks that display printer information, allowing unauthorized users to request temporary printing or cancel watermarks, ensuring secure document printing without disrupting normal office operations.
Device Control
Device Control module can control the usage permissions of various client devices such as storage, communication, USB, etc., and can also restrict the transmission of files from mobile smart terminals, prohibit ADB mode access, and manage burning behavior. Users without relevant permissions can apply for or register temporary use of equipment and burning functions to meet the needs of enterprise equipment management and data leakage prevention.
Removable Media Control
Removable Media Control module can record the access and document operation information of mobile storage, register and authorize USB flash drives, and turn ordinary USB flash drives into encrypted disks and automatically encrypt stored documents. Unregistered or unauthorized mobile storage cannot be used. When the terminal disables mobile storage, users can apply or register for use, helping enterprises manage mobile storage and prevent data leakage.
Instant Message Monitoring
Instant Message Monitoring module can fully record conversation information of mainstream instant messaging tools, and can also control outgoing documents and back up outgoing files by document name and size. When the terminal disables IM file transmission, users can apply for approval or filing before sending, helping enterprises monitor IM communication and prevent illegal file transmission.
Email Control
Email Control module can record the sender, recipient, body and attachment information of various types of emails, and can also control outgoing emails according to conditions such as sender, recipient, attachments, etc. It also supports setting up forced carbon copies. When the terminal is disabled for sending emails, users can apply for approval or filing before sending, helping companies to manage email exchanges and prevent illegal outgoing information.
Web Access Control
Web Access Control module records the URLs and titles of web pages browsed by each computer in detail, and provides statistics on browsing activity using lists and charts. It also controls website access by designated clients at specific times and prohibits network uploads using various protocols. If a terminal is unable to upload web pages, users can apply for approval or file a record before uploading, helping businesses monitor web activity and prevent file upload leaks.
Network Access Control
Network Access Control module can limit network access permissions by application, network address, etc., and can also control network communications between clients and external computers.
Network Traffic Control
Network Traffic Control module can count the network traffic within the client's specified time, and can be classified by address, protocol, etc. or counted by computer. It can also limit traffic by address, port, etc. to help enterprises make rational use of bandwidth.
Application Control
Application Control module can record operations such as application startup and exit and count usage. It can limit program execution by time, manage software installation and uninstallation, and display watermarks on the computer screen to help companies monitor software usage, prevent illegal installation and uninstallation, and prevent leaks through photography.
Sensitive Content Inspection
Sensitive Content Inspection module can customize sensitive information rules, discover sensitive files through local and remote scanning, automatically label documents containing sensitive content with confidentiality levels, monitor the clipboard, file transmission and landing behaviors, block, audit and log operations that violate the regulations on the transmission of sensitive content. Users can apply or file for permission when they do not have permission to transmit it, but the decryption warning function requires the additional purchase of related modules.
IT Asset Management
IT Asset Management module can automatically scan and record terminal software and hardware assets and change information, scan and install Microsoft patches, detect system vulnerabilities and provide solutions, and automatically distribute and install software (supports breakpoint resumption and elevated installation) and batch uninstall illegal software.
Transparent Encryption
Transparent Encryption module uses high-strength technology to transparently encrypt documents. Automatic decryption remains unaffected in trusted environments, while untrusted environments prevent opening. It also prevents content theft via clipboard or screenshots, and offers three encryption modes: mandatory, intelligent, and read-only. Encrypted documents can be divided into security zones and levels of confidentiality, with access permissions and outbound rules set. It supports offline authorization, multi-channel application approval, and mobile operation. However, the offline USB key and USB flash drive encryption client must be purchased separately. Disaster recovery mechanisms are also available to ensure system operation and document backup.
Cloud Document Backup
Cloud Document Backup module can back up terminal documents in real time or periodically, and also supports full disk scanning and batch backup. It can set backup strategies based on document type, size, etc., and can avoid storage redundancy by judging document content. At the same time, it can manage backup copies, find backup files, and assign operating permissions. When disk space is insufficient, it will issue an alarm or automatically clean up. It will also record logs of document backups and administrator operations, making it easier for enterprises to manage backup documents and ensure data security.
Document Tagging
Document Tagging module allows you to manually label and assign classification levels to documents (e.g., technical documents, confidentiality level), or automatically assign classification levels based on sensitive content or document type (requires the purchase of the Sensitive Content Identification Module). Documents with classification levels can be audited and blocked when sent externally (requires the corresponding control module), and encrypted upon delivery (requires the Document Transparent Encryption Module). It also displays classification level reminders in Office/WPS and records relevant operation logs. It supports multiple document types, including Office, WPS, and PDF.
Watermarking & Document Tracing
Watermarking & Document Tracing module can add a variety of watermarks (text, images, QR codes, etc.) to documents, pictures, printouts, and even computer screens. It also supports adding invisible watermarks to pictures that are invisible to the naked eye. Users can remove watermarks manually or by applying for registration, and transmit the documents without watermarks. Watermarks or flow information will be automatically added when the document is transmitted, landed, or decrypted. Watermarks can also be added when printing, and the watermark operation log will be recorded. However, some transmission-related functions need to be implemented in conjunction with other modules.
Screen Monitoring
Screen Monitoring module can view the screenshots of a single client in real time, monitor the screen images of multiple users (including multiple monitors) at the same time, and record the historical screen images of the client (recorded by application frequency conversion). The corresponding screen can be viewed in conjunction with the log, and it also supports the conversion of historical screens into general video playback.
AI Visual Perception
This module uses a proprietary AI model to access the computer's camera. It can detect abnormal user behavior, camera obstruction, and external monitor use in real time. When triggered, it locks the computer, issues an alarm, and logs the activity. When enabled, the desktop displays a notification indicating the camera is active. It supports multiple unlocking methods, including face recognition and button clicks. It also records a video log of employee actions such as viewing privacy policies, taking photos with their phone, and attempting to unlock the device.
Remote Maintenance
This module can view the client's application, process and other operating information in real time, making it convenient to remotely analyze the cause of the fault and solve the problem. After the administrator applies and the user agrees, the terminal desktop can be remotely connected to provide assistance or operation demonstrations, and the client folder can be remotely opened to transfer files and collect fault samples.
Secure Access Gateway
This hardware security gateway can prohibit illegal computers from accessing protected servers. Encrypted documents uploaded by terminals to the server will be automatically decrypted, and documents downloaded from the server will be automatically forced to be encrypted. It also supports multi-system terminals and enterprise servers of various architectures. Computers must install the AnySecura client or be on the IP/MAC whitelist to access the server. Unqualified access will jump to a warning page. It has ByPass disaster recovery function and supports both serial and bypass deployment methods without changing the network structure.
Security Audit Reports
This smart risk audit report can statistically analyze intranet computer operation behaviors from multiple dimensions such as printing, email, and mobile storage, and use trend tables to show the changing trends of user behavior. It also has a graded risk sign warning mechanism. When the behavior reaches the threshold, it will automatically record the event and remind the management personnel, helping to understand the intranet situation and optimize the management and control strategy.
Proactive Risk Alerts
The AnySecura "Data Analysis and Early Warning Platform" module focuses on three core areas: risk warning, data security, and terminal management. Each function requires collaboration with its corresponding module.
The Early Warning Center leverages the Document Operations Control module to aggregate and analyze risk events, personnel, and details, and allows for customized early warning rules. This module is also required for data security (decryption logs require the additional purchase of the Document Transparent Encryption Module), which provides statistics on document transfers, tracks derivatives, and enables traceability. Terminal management integrates the Asset Management and Application Control modules to analyze software usage and authorizations, and supports software library configuration, comprehensively covering risk, data, and terminal software management needs.
Secure Document Exchange
The AnySecura secure document exchange system focuses on "secure transfer + compliance management" and is divided into six major modules. First, "Security Domains" isolate networks, set access permissions, and clarify data boundaries. "Document Exchange" supports cross-domain and intra-domain transfers, group sharing, and external links. It also controls preview and download permissions, adapting to various collaboration scenarios.
"Exchange Approval" allows for customized processes and whitelisting for efficiency. "Personal Space" provides dedicated storage and large file handling. An integrated encryption module enables upload decryption and download encryption. Finally, "Security Audit" logs the entire process for easy traceability.
Forcepoint vs AnySecura: Which DLP Wins?
Forcepoint DLP is suitable for enterprises that have already implemented basic endpoint and network protection and only need to deploy specialized data protection for cloud and web channels. It can serve as an efficient "guardian" for specific channels.
For most enterprises seeking a forward-looking, comprehensive, and deeply integrated data security strategy, AnySecura is a better choice. Its platform-based approach covers endpoint control, user behavior monitoring, refined content detection, and high-strength encryption. It can address data risks across multiple dimensions, including personnel, technology, and operations, to build a comprehensive protection system. Compared to channel-focused protection, AnySecura strengthens data security from the bottom up, comprehensively protecting the entire data ecosystem and better meeting enterprises' long-term data security needs.


