As enterprise digitalization accelerates, massive volumes of documents are now scattered across countless endpoint devices. Even more concerning, files can be transferred through USB drives, cloud storage, email, instant messaging tools, or web uploads—sometimes containing sensitive information hidden in images or unmarked documents.
The result: Increasing risks of accidental or intentional data leaks.
- How can sensitive information be accurately identified among massive amounts of documents?
- Once sensitive content is identified, how can it be effectively controlled and protected?
How AnySecura Helps Enterprises Safeguard Sensitive Data
AnySecura Data Loss Prevention (DLP) solution leverages advanced sensitive content recognition to help organizations protect critical assets across endpoints. Based on document sensitivity, the system can automatically apply appropriate security controls, including:
- Encryption
- Outbound transfer restrictions
- Risk-triggered screen recording
- Behavior auditing
This multi-layered approach significantly strengthens enterprise data protection capabilities.
How to Build an Intelligent Data Protection System (Four Steps)
1. Lock Down Sensitive Documents
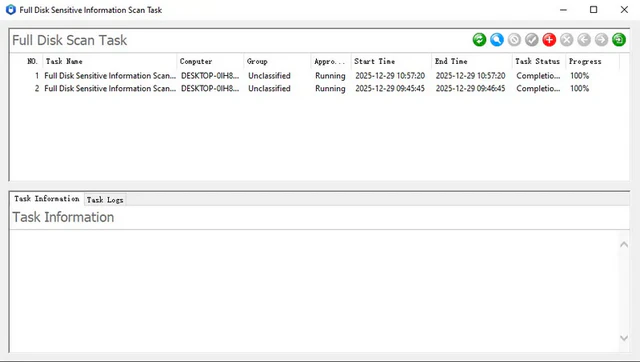
Comprehensive scanning and precise identification: Using AnySecura's sensitive content scanning tool, organizations can perform a full scan across endpoint devices to quickly locate documents containing confidential or sensitive information that requires protection.
Automatic encryption and dynamic protection: For sensitive documents that are not yet encrypted, the system can automatically trigger AnySecura document encryption, ensuring that sensitive data is protected with strong encryption.
Source-level protection across the entire lifecycle: Whenever users create or edit sensitive documents—or download them from servers—the system can automatically encrypt the files. Security policies can also adjust document classification levels or add visible and invisible watermarks, ensuring sensitive information remains protected throughout its entire lifecycle and preventing unauthorized redistribution.
2. Block Data Leakage Channels
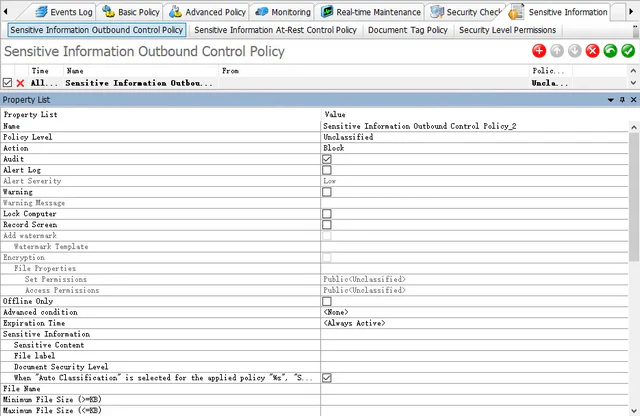
Real-time blocking of risky behaviors: AnySecura integrates sensitive content recognition with endpoint control policies. When documents containing sensitive information are transferred via USB drives, cloud storage, instant messaging tools, email, or web uploads, the system can automatically detect and block these actions in real time.
Traceable evidence for approved transfers: For documents that are approved for external sharing, AnySecura can automatically create backup copies and add document watermarks containing information such as the user identity and timestamp. If a leak occurs, organizations can quickly trace the source and provide solid evidence for security audits—creating a strong deterrent against potential insider threats.
3. Capture Only Critical Moments
No more unnecessary screen recording: Instead of recording all user activity indiscriminately, AnySecura focuses on high-risk behaviors, eliminating unnecessary storage usage.
Risk-triggered screen recording: When the system detects sensitive documents being transferred through channels such as removable storage, cloud drives, instant messaging, email, printing, or web uploads, it automatically triggers screen recording to capture the exact moment the sensitive data is being transferred.
Improved audit efficiency: This risk-driven recording approach significantly reduces storage costs while ensuring precise and efficient auditing. Every critical operation involving sensitive data can be clearly traced.
4. Get Full Visibility into Sensitive Data Movement
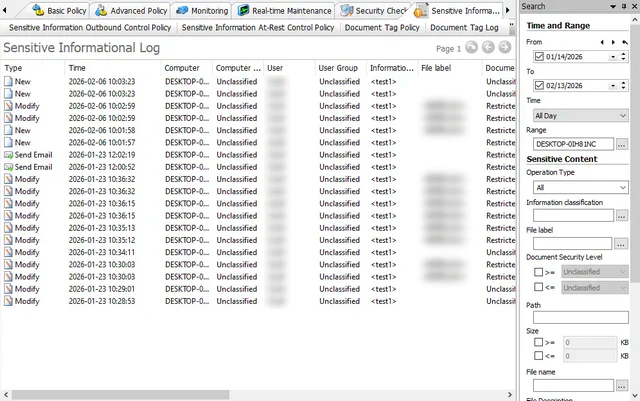
Complete process logging: AnySecura records detailed logs of sensitive content scans, encryption status, and every outbound transfer attempt involving sensitive documents.
Multi-dimensional analysis: With AnySecura's risk audit reports, data dashboards, and analytics-based alerting systems, organizations can monitor trends in sensitive document transfers across multiple dimensions. This enables security teams to quickly identify potential risks and respond promptly, while also providing valuable insights for continuously optimizing enterprise security policies.
Conclusion
Starting from sensitive content inspection, AnySecura builds a complete lifecycle protection framework—covering inspection, encryption, control, and traceability. Enterprises can prevent unauthorized access and external transfer of sensitive documents, significantly reducing the risk of data leakage at its source.
Take action now: Ready to take your enterprise security to the next level and prevent data leaks? Contact our team today to protect your most valuable information.






