Looking for an endpoint security tool to protect your company from cyber risks? SentinelOne is often considered a strong option, especially with its recent AI-driven capabilities. If you’re evaluating whether it’s the right fit for your organization, this article will help you make a clear decision—covering what SentinelOne does well, where it may fall short, and how it compares to other leading solutions.

What Is SentinelOne and How Does It Work?
What Is SentinelOne?
Classic antivirus focuses on known malicious files. However, modern attacks may not look like a “virus.” Many firms now buy endpoint detection and response (EDR) so they can handle the unknown threat.
SentinelOne, Inc. sells SentinelOne as part of this shift. In simple terms, SentinelOne EDR watches device behavior, ties related events together, and can take action fast with less human input. That matters when you face ransomware, short staffing, or lots of remote laptops.
You will also hear XDR in its introduction. XDR is basically EDR plus more signals (for example cloud and identity), so teams can spot linked attacks across more places. The goal is fewer blind spots and faster response.

How SentinelOne Detects and Responds to Threats
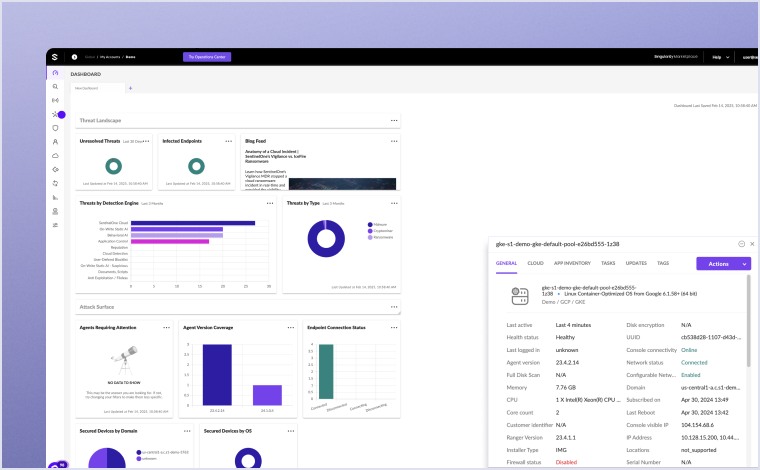
SentinelOne uses a “Sentinel” agent on each endpoint and a globally available SaaS console to manage policies and see alerts. It uses static and behavioral AI. Static checks help spot known bad files. Behavioral checks watch what processes do over time, which helps detect ransomware, zero-days, and fileless attacks.
Its agents can apply prevention and detection with or without cloud connectivity, which is useful for remote laptops that go offline.
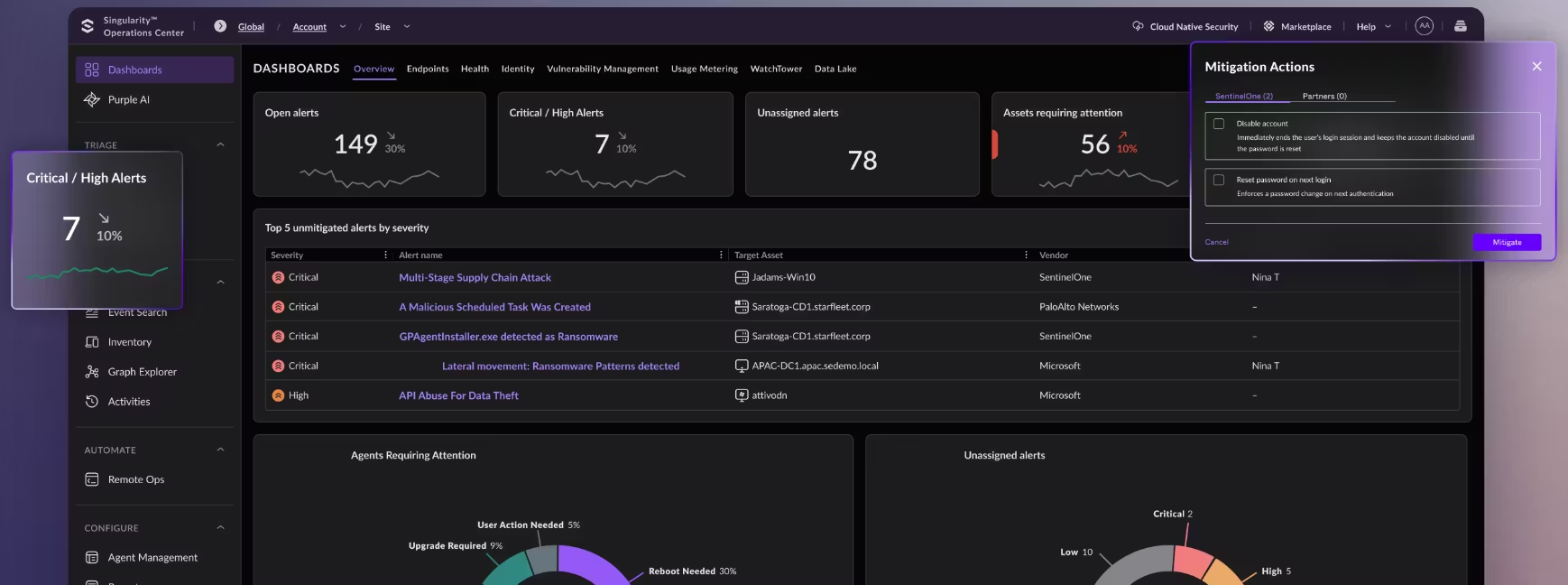
Response is where EDR earns its keep. SentinelOne says endpoints can kill and quarantine unauthorized processes and files in real time, and it offers both automated and manual remediation actions.
SentinelOne Features: What You’re Really Buying
- Autonomous Security (Less Manual Work): Detects and responds to threats automatically, reducing reliance on analysts and enabling machine-speed protection.
- Faster Detection and Response: AI-driven detection and automated remediation significantly reduce incident response time and limit attack impact.
- Strong Protection Against Unknown Threats: Uses behavioral AI to detect zero-day attacks, fileless malware, and advanced ransomware beyond signature-based tools.
- Built-in Ransomware Rollback: Restores infected systems to a clean state after an attack, minimizing downtime and operational disruption.
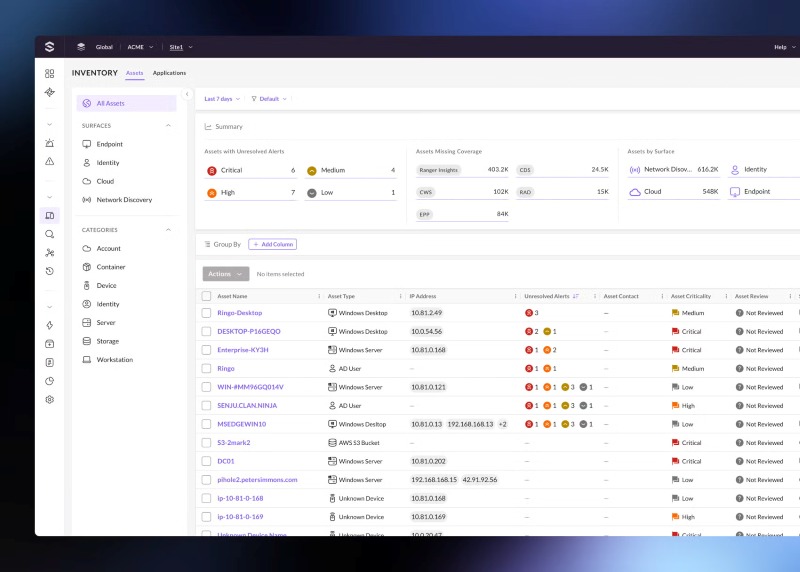
- Full Visibility Across Environment: Provides deep visibility into endpoints, cloud workloads, and identities from a centralized console.
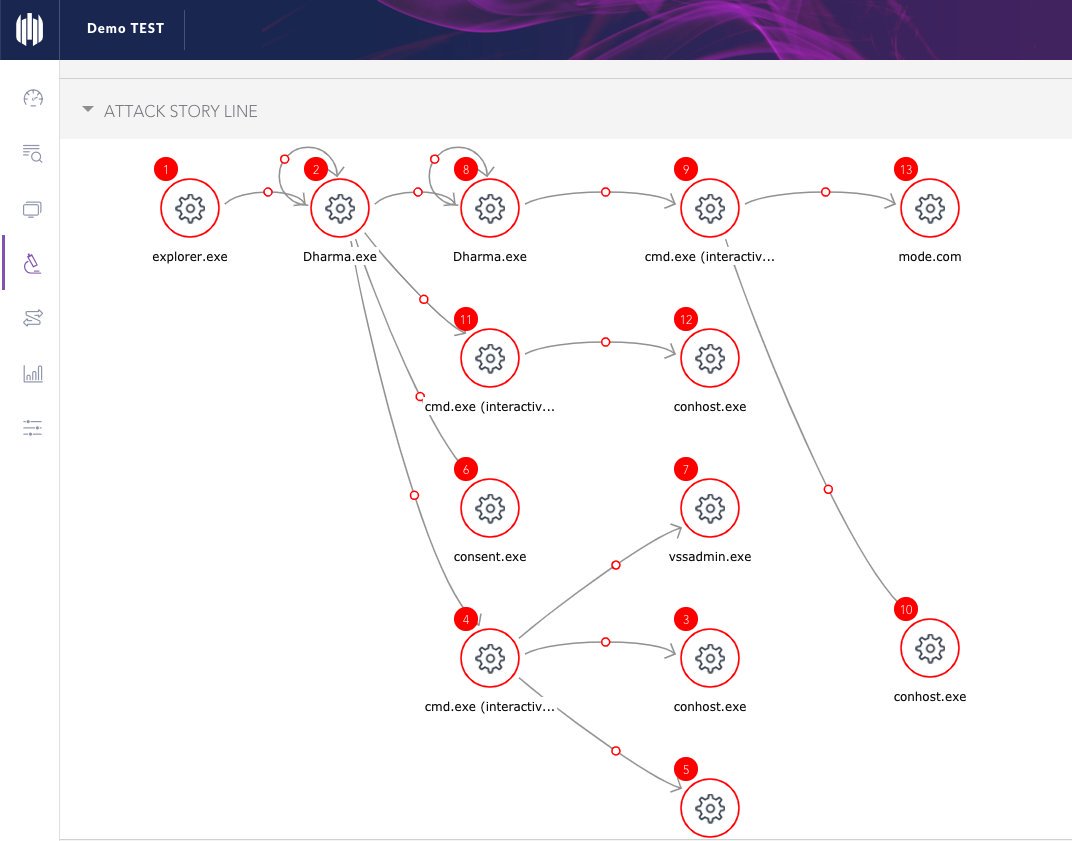
- Better Context for Investigation (Less Noise): Correlates events into a single attack storyline, reducing alert fatigue and speeding up root cause analysis.
- Unified Platform (Fewer Tools to Manage): Combines EPP, EDR, and XDR capabilities into one platform, simplifying security operations.
- Scales Easily Across Organizations: Cloud-native design and automation allow deployment from small teams to large enterprises without heavy SOC overhead.
- Improved Security Efficiency and ROI: Reduces operational costs through automation, fewer alerts, and faster remediation.
- Easy to Use for Security Teams: Intuitive interface and clear telemetry make investigation and response more efficient, even for smaller teams.
SentinelOne Pros and Cons: Is It Worth It?
Why Choose SentinelOne: Key Advantages Explained
Reduce Dependence on Large Security Teams
SentinelOne’s biggest practical advantage is automation. It can detect and respond to threats without constant analyst involvement, which directly reduces workload. If your team is already stretched or you don’t want to scale headcount alongside security needs, this becomes a decisive factor.
Minimize Impact from Ransomware and Fast-Moving Attacks
In a real breach, success depends less on spotting the intruder and more on how soon you isolate the damage plus return to normal. SentinelOne reacts the moment it senses hostile code - it halts the process, records every change then reverses those changes in the same sequence they occurred. Systems return to their last clean state within minutes - services stay up, fewer records vanish and revenue keeps flowing. Firms that lose money each minute their sites stay down value such speed.
Detect Modern Threats That Traditional Tools Miss
Traditional antivirus products that rely only on known signatures miss many modern intrusions. SentinelOne deploys behavioral artificial intelligence to uncover zero day exploits, fileless infections and sophisticated ransomware strains. Organizations that abandon outdated antivirus suites or improve endpoint protection often select SentinelOne for this capability.
Improve Visibility and Speed Up Investigation
Security teams often waste time correlating alerts across multiple systems. SentinelOne's Storyline method links every event that occurs during an intrusion into one continuous, chronological record of the attack. Security staff see the whole sequence in one place - they grasp the situation fast and act without delay. Less time is spent on manual data correlation plus choices about containment and remediation gain clarity.
SentinelOne Limitations: Where It May Not Fit
Higher Cost Compared to Simpler Endpoint Tools
SentinelOne operates as a complete EDR/XDR platform, far beyond the scope of conventional antivirus software. The advanced capability brings elevated licence fees and, in many cases, extra charges for data retention and third party connectors. A modest team or a budget constrained organisation whose sole need is simple endpoint defence often finds such a product excessive.
Requires Security Maturity to Fully Utilize
While automation reduces workload, SentinelOne still produces rich telemetry and advanced features that require security knowledge to interpret properly. Without a defined incident response process or experienced personnel, organizations may not fully benefit from its capabilities.
Not a Complete Security Stack on Its Own
SentinelOne handles detection and response for endpoints, server workloads plus user identities. The platform does not take over email protection, network controls or systems that stop data from leaving the organization. A company must keep additional security layers in place - the overall security design remains intricate.
Cloud and Data Retention Costs Can Increase Over Time
Heavy dependence on long term data retention or integration with SIEM/SOAR platforms raises expenses because of storage requirements and data ingestion. Compliance focused environments that mandate extended logging face the sharpest impact.
Limited Visibility into User Intent and Data Context
SentinelOne excels at spotting hostile actions within a workstation or server but the agent lacks built in logic to interpret the business meaning of the data it guards. The platform warns when code behaves like ransomware or when a process spawns unexpected scripts but it does not judge whether a spreadsheet marked "confidential" leaves the network through a personal mailbox. That sort of judgment - deciding if a specific document violates corporate policy when it moves - belongs to data-loss-prevention suites and insider risk platforms that map files to owners, owners to roles and roles to permitted destinations.
While EDR stops external hackers, it won't stop an employee from leaking a file. This is why we recommend layering AnySecura’s Data Loss Prevention over your EDR.
SentinelOne Pricing: Cost, Plans, and Licensing Explained
According to the official website, pricing for the Singularity platform is structured as follows (annual, per endpoint):
- Core: $69.99 per endpoint/year
- Control: $79.99 per endpoint/year
- Complete: $179.99 per endpoint/year
- Commercial: $229.99 per endpoint/year
- Enterprise: Custom pricing (contact sales)
While the Core and Control tiers look cheaper, they mainly replace traditional antivirus. Most organizations evaluating SentinelOne for real security outcomes (EDR, automation, threat visibility) end up choosing the Complete tier. This is where full detection, response, and investigation capabilities are available.
In practice, companies rarely pay full list price. Discounts are common depending on deal size and partner relationships. A typical range for the Complete tier is around$120–$160 per endpoint per year, though this varies by region and negotiation strength.
The base license is only part of the total cost. Many organizations add:
- MDR (Managed Detection & Response) for 24/7 monitoring
- Extended data retention for compliance and forensics
- Advanced AI or threat intelligence features
These additions can significantly increase total cost, sometimes pushing effective pricing above $200+ per endpoint/year in enterprise environments.
SentinelOne vs Competitors: How Does It Compare?
SentinelOne has several competitors in the same category. If you feel it may not be the right fit for your environment, this comparison can help you find a more suitable alternative based on your needs.
| Category | SentinelOne | CrowdStrike | Microsoft Defender |
|---|---|---|---|
| Core Strength | Automation and autonomous response | Threat intelligence and analyst-driven workflows | Deep integration with Microsoft ecosystem |
| Detection Approach | Behavioral AI with automated actions | Cloud intelligence + threat hunting | Behavior + signatures + Microsoft signals |
| Response Speed | Fully automated (fastest response) | Semi-automated (often analyst-driven) | Partially automated (depends on setup) |
| Ease of Operation | Easy to run, less manual effort | Requires skilled team | Requires configuration and tuning |
| Visibility & Context | Strong (Storyline attack view) | Strong (deep telemetry + intelligence) | Strong (within Microsoft ecosystem) |
| Best Fit | Lean teams, automation-first environments | Mature SOCs needing deep intelligence | Microsoft-heavy organizations |
| Cost Positioning | Mid-range | High | Low to mid (often bundled) |
| Main Trade-off | Less focus on external threat intelligence | More manual work and higher cost | Limited outside Microsoft ecosystem |

Explore the top CrowdStrike competitors in 2026. Compare 10 alternatives by use case and features to choose the right fit. Learn more>>
- If you want to reduce manual work and rely on automation, SentinelOne is usually the better fit.
- If you have a mature security team and want deeper threat intelligence, CrowdStrike is a stronger option.
- If your environment is already built around Microsoft and you want to control cost, Microsoft Defender is often the most practical choice.
Complete Your Security with SentinelOne and AnySecura
After choosing SentinelOne, you’ve addressed endpoint threats—but not how sensitive data is used by legitimate users. In many environments, data leakage happens through normal actions like file uploads, external sharing, or USB transfers, which EDR tools are not designed to control. This is where AnySecuracomplements the setup by enforcing data usage policies, encryption, and user behavior controls. If your goal is to reduce both security incidents and data leakage risk, combining the two is a practical and complete approach.
Use SentinelOne for Threat Detection, AnySecura for Data Control
SentinelOne is strong at detecting and stopping threats on endpoints—malware, ransomware, suspicious behavior. But it does not control how sensitive data is used after access is granted. This is where AnySecura fits in. It focuses on data protection—controlling file access, encryption, and user behavior. Together, they cover both threat prevention and data protection, which are usually handled separately.
Combine Endpoint Detection with Data Loss Prevention
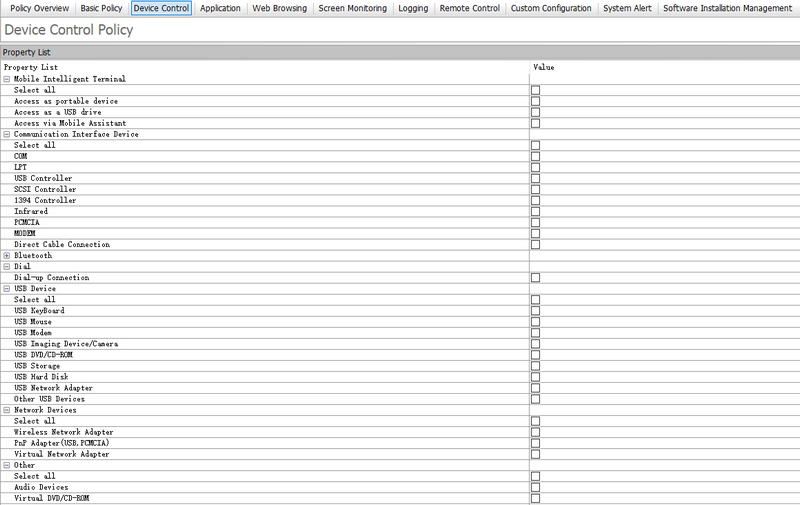
SentinelOne can tell you when something malicious is happening on a device. AnySecura can control what users can do with sensitive data on that device. For example, even if a device is not compromised, data can still leak through USB drives, uploads, or messaging tools. AnySecura’s Device Control, Web Access Control, and Email Control help prevent this. This combination closes a common gap: attacks vs internal data misuse.
Use Transparent Encryption to Protect Data at Rest and in Use
SentinelOne protects the system, but it does not encrypt business files by default. AnySecura’s Transparent Encryption ensures that sensitive files remain encrypted automatically based on policies (file type, user group, location). Authorized users can still work normally, while unauthorized access results in unreadable data. This is especially important if endpoints are lost, stolen, or accessed improperly.
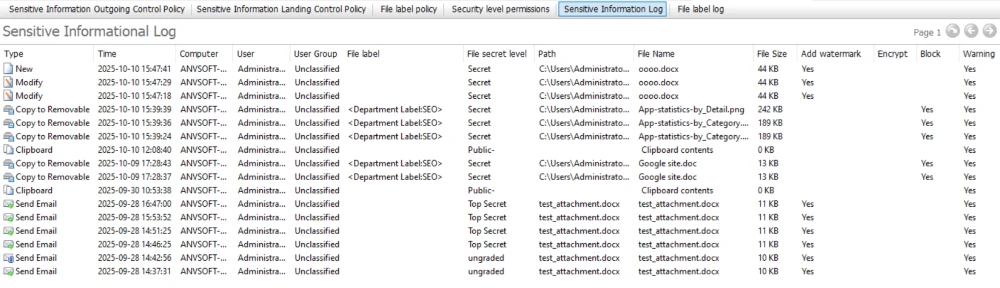
Improve Incident Response with Data Context
When SentinelOne detects suspicious activity, it shows what happened at the system level. AnySecura adds another layer—what data was involved. With features like Sensitive Content Inspection and Document Tagging, you can understand whether the activity involved critical business data. This helps prioritize incidents and respond based on actual risk, not just technical alerts.
Control What Happens After a File Is Opened
Most security tools stop at access control. AnySecura goes further by controlling actions after a file is opened. You can restrict copying to USB, uploading to websites, or sending via email—even for authorized users. This is important because many data leaks happen after legitimate access, not during a breach. SentinelOne cannot control this layer, but AnySecura can.
FAQs about SentinelOne
1. Is SentinelOne better than CrowdStrike?
It depends on your environment and budget. Both are strong EDR vendors, so run a pilot and compare alert quality, response speed, and total operating cost.
2. Who should use SentinelOne?
Mid-size and large organizations that need strong endpoint response and can operate an EDR program. It is most valuable when ransomware downtime risk is a priority.
Conclusion
If your concern is purely malware, ransomware, and endpoint detection, SentinelOne is a solid choice. It gives you automated response, behavioral detection, and good visibility into endpoint threats.
If your goal is real enterprise protection, you don’t just need to stop attackers. You need to control what happens after access is granted.
👉 Pair SentinelOne with AnySecura to close that gap, protect endpoints and the data that actually matters.


