AI risks are no longer new—or hypothetical. With hundreds of vulnerabilities reported in OpenClaw and incidents like Meta exposing sensitive data internally, the consequences are already here.
Embracing AI in production is no longer just a technical challenge—it’s a security challenge. And AI security solutions are quickly becoming the foundation for scaling AI responsibly.
If your team is already asking:
- Can we see how AI is being used internally?
- Can our AI systems survive under real attack scenarios?
This article highlights 9 mature and leading AI security solutions, helping you map your concerns to the right categories, and identify what actually fits your business.

Top 9 AI Security Solutions to Protect Your Team in 2026
Top 9 AI Security Solutions: Quick Overview
| Solution | Category | Best For | Key Strength | Limitation |
|---|---|---|---|---|
| AnySecura | AI usage security | Enterprises with widespread employee use of GenAI tools | Real-time visibility and control over AI usage | Does not cover model-level security |
| Protect AI Guardian | Model security | Enterprises handling model artifacts | Deep model scanning across formats | Less useful for API-only AI users |
| HiddenLayer AISec Platform | AI detection/response | Large AI estates needing runtime oversight | Broad lifecycle coverage with runtime security | Heavier platform fit |
| Mindgard | AI red teaming | Teams needing continuous adversarial testing | Realistic attacker emulation | Testing tool, not complete protection by itself |
| Cranium | AI governance / AISPM | Enterprises needing inventory, compliance, and evidence | Strong governance and posture focus | Not an inline runtime control first |
| Zenity | AI agent security | Organizations deploying tool-using AI agents | Purpose-built agent visibility and control | Less relevant for non-agent AI programs |
| Microsoft Purview DSPM for AI | AI data protection / governance | Microsoft-centric enterprises | Deep Microsoft integration | Weaker fit outside Microsoft ecosystem |
| Lakera Guard | LLM security | Teams deploying LLM apps fast | Strong prompt-injection focus | Narrower than full-platform tools |
| Robust Intelligence AI Firewall | AI application security | Enterprises wanting runtime validation and filtering | Mature AI firewall approach, now with Cisco scale | Overlaps with other runtime guardrail tools |
1. AnySecura
AnySecura addresses one of the most practical problems for enterprises: As employees and developers increasingly use generative AI tools in browsers, IDEs, desktop applications, and APIs—both sanctioned tools and “Shadow AI”—sensitive documents and confidential data are often fed directly into prompts.

AnySecura operates across browsers and desktop applications, giving security teams real-time visibility into which AI tools employees are using and what they input, policy-driven controls to block sensitive actions, and automated enforcement to prevent policy violations. It includes features such as:
- Real-time AI usage monitoring: Track how employees or applications are calling GenAI to detect abnormal behavior or risks.
- Shadow AI discovery: Identify unauthorized or uncontrolled use of AI tools.
- Sensitive data masking/interception: Automatically block or prevent sensitive data from being uploaded before it reaches the AI model, protecting internal data and personal information.
- Support for multiple GenAI tools and models: Not tied to a single vendor; can integrate with different AI platforms.
- SaaS or on-premises deployment: Choose the deployment method that fits the enterprise’s needs.

It is more focused on usage-side and application-side governance and does not perform security scanning of model files themselves. Enterprises that download large numbers of third-party model files still need tools like Guardian to supplement security checks.
 Suitable For
Suitable For- Enterprises where employees widely use ChatGPT, Claude, Gemini, or AI coding assistants, and need full visibility, policy control, and audit records.
- Organizations that want to protect both employee AI usage
- Companies looking to implement real-time "red line" controls and guided training with low latency and minimal disruption.
 Not Suitable For
Not Suitable For- Organizations where AI usage mainly involves self-hosted inference or importing model files
- Employees rarely use public generative AI tools.

Learn what data leakage in machine learning is, why it happens, and how to prevent it.Learn more>>
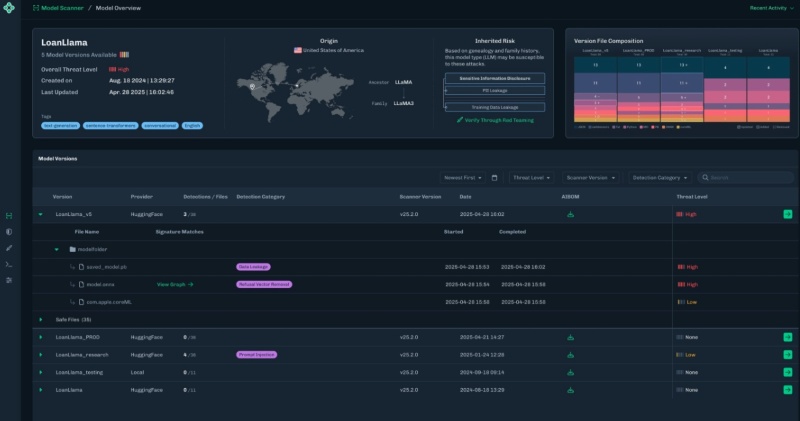
2. Protect AI
Protect AI Guardian is most relevant for ML platform teams, MLOps teams, and security teams handling third-party or internally shared model assets. Its role is to perform security scans on model files and formats before a model enters development or production environments. If your team are mainly using APIs (e.g., OpenAI, Claude), you may want to consider it.
Guardian has incomparable format coverage and supply chain scale: official materials emphasize that it can scan 35+ model formats (including PyTorch, TensorFlow, ONNX, Keras, Pickle, GGUF, Safetensors, etc.) and can detect deserialization attacks, architectural backdoors, and runtime threats.
The second advantage is its role as an "online scanning partner" in the open-source model ecosystem: Hugging Face official documentation states that it collaborates with Protect AI to provide Guardian scanning and frontend security reporting for files in public Hub repositories.
A public Hugging Face article disclosed that as of April 1, 2025, Protect AI had scanned approximately 4.47 million unique model versions across about 1.41 million repositories, identifying numerous suspicious or unsafe issues.
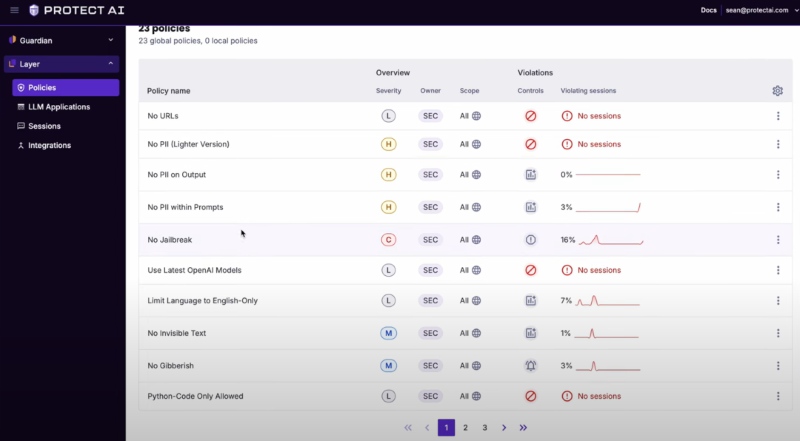
However, it cannot replace LLM runtime guardrails (such as prompt injection, output leakage, or unauthorized tool calls), nor is it equivalent to connecting AI interaction logs to a SOC via AIDR. Enterprises typically integrate Guardian into CI/CD or MLOps gates while deploying runtime protections in parallel.
 Suitable For
Suitable For- Enterprises that heavily use third-party or open-source models
- Organizations with frequent model imports and mature MLOps workflows that are willing to treat scanning as a "model release gate."
- Security teams aiming to include "model supply chain security" in MLSecOps
 Not Suitable For
Not Suitable For- Teams that rarely imports model files or trains models directly.
- Teams that need to address runtime prompt attacks and output compliance
3. HiddenLayer AISec Platform
HiddenLayer is an AI detection and response platform. It focuses on protecting AI systems in production by providing visibility into model behavior, detecting attacks, and enabling response actions. It is particularly for enterprises that treat AI systems as operational assets—requiring continuous monitoring, telemetry, and incident response.
Its biggest strength is lifecycle breadth anchored by runtime defense. HiddenLayer is not just selling one scanner or one filter, it offers discovery, model validation, runtime monitoring, and attack simulation in one platform. So if you have multiple AI systems in production and a team that can actually operate these signals, you may find it attractive.
The downside is complexity. A platform with discovery, runtime detection, and attack simulation makes more sense in enterprises with many AI assets and a dedicated security function. Smaller teams or firms still in early experimentation may find it heavier than they need, especially if they only have a few LLM applications and want one focused control.
 Suitable For
Suitable For- Larger enterprises with multiple AI systems in production
- SOC and security engineering teams that want AI-specific monitoring
- Regulated industries that need operational oversight
 Not Suitable For
Not Suitable For- Small teams with only a single pilot chatbot
- Buyers wanting the cheapest point solution
- Organizations without staff to operationalize runtime signals
4. Mindgard
Mindgard is for organizations that want to identify weaknesses in their AI systems through adversarial testing. Its core role is to emulate adversaries and continuously test AI systems, agents, tools, data flows, and workflows for exploitable weaknesses. That makes it most useful for organizations that want to assess resilience before and after release, rather than only block threats live in production. Traditional penetration testing rarely covers the strange failure modes of LLMs, RAG systems, and agents; Mindgard is built specifically for that gap.

Its biggest advantage is realism of testing. Mindgard emphasizes attacker emulation and a broad attack library spanning jailbreaks, prompt injection, model inversion, extraction, poisoning, and evasion. For security leaders who want evidence of how an AI system fails under pressure, this is often more valuable than a simple policy checklist.
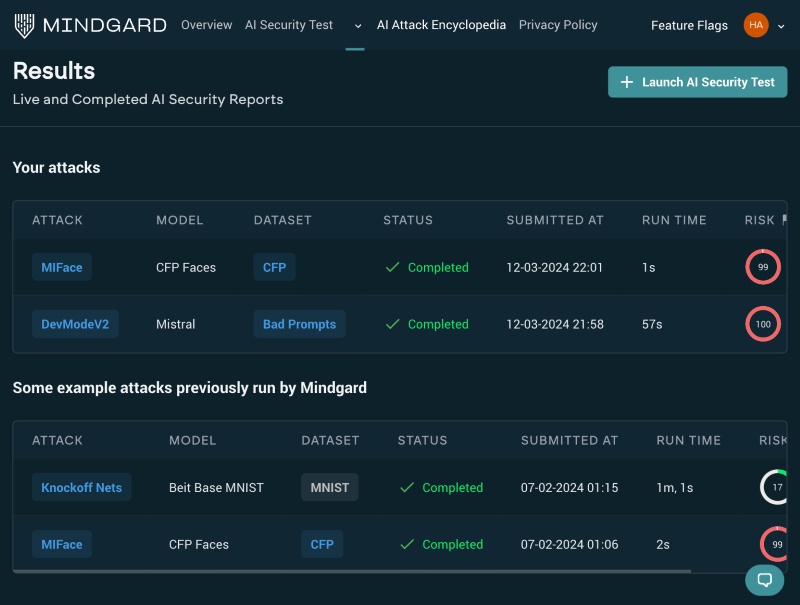
The limitation is that red teaming is a testing capability, not a full-time protective layer by itself. It helps you find and prioritize weaknesses, but it does not replace runtime controls, data protection, or governance. It also assumes you have the engineering discipline to fix what it finds; otherwise, you just accumulate findings.
 Suitable For
Suitable For- Enterprises with active AI release cycles
- Security teams that want continuous validation
 Not Suitable For
Not Suitable For- Teams without bandwidth to remediate issues
- Companies looking only for day-to-day runtime blocking
5. Cranium
Cranium is best for AI usage visible and governable inside the enterprise. This becomes necessary when AI usage spreads across teams and your team need to discover AI systems, build an inventory of models and applications, and document how they are used. This is especially useful for risk, compliance, and governance teams. In many companies, AI adoption is growing faster than oversight—teams may be using internal models, third-party APIs, or embedded AI features without a clear record of what exists or how it is controlled. Traditional GRC tools were not built with AI assets, model lineage, AI BOMs, or AI-specific regulatory mappings in mind; Cranium is trying to fill that operational gap.
Instead of static documentation, Cranium continuously discovers AI systems, maintains an up-to-date inventory, maps controls to compliance frameworks, and generates audit-ready evidence, which is exactly what large enterprises need as AI use spreads across teams and vendors. This is especially useful for organizations preparing for formal scrutiny under frameworks like NIST, ISO, or the EU AI Act.
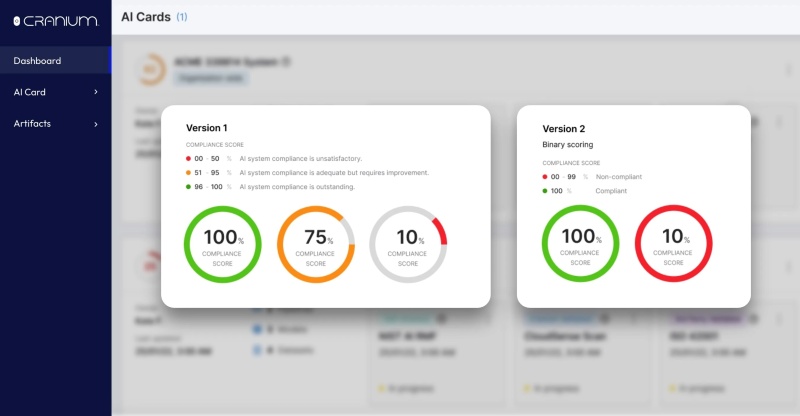
Cranium can help you see, document, and manage AI risk, but it is not the first answer to prompt injection on a live chatbot or malicious model artifacts entering an MLOps pipeline.
 Suitable For
Suitable For- Large enterprises with many AI initiatives
- Regulated organizations facing audits or policy requirements
- Risk and compliance teams that need AI inventories and evidence
 Not Suitable For
Not Suitable For- Small firms with only one or two AI pilots
- Teams whose main gap is runtime blocking
6. Zenity
Zenity is one of the clearest examples of the new agent-security segment. Its platform focuses on discovering agents, monitoring what they can access, and enforcing policy from build time to runtime across SaaS, cloud, and endpoint environments. That matters because AI agents are not just answering questions; they are starting to take actions, call tools, access business systems, and move data. Traditional appsec and identity tools do not fully model that new risk pattern.
Many enterprises are moving from chatbots to agents, and Zenity is built around that exact transition. The product’s emphasis on discovery, inventory, behavior monitoring, and inline controls gives security teams a more agent-centric view than general-purpose AI security products usually provide.
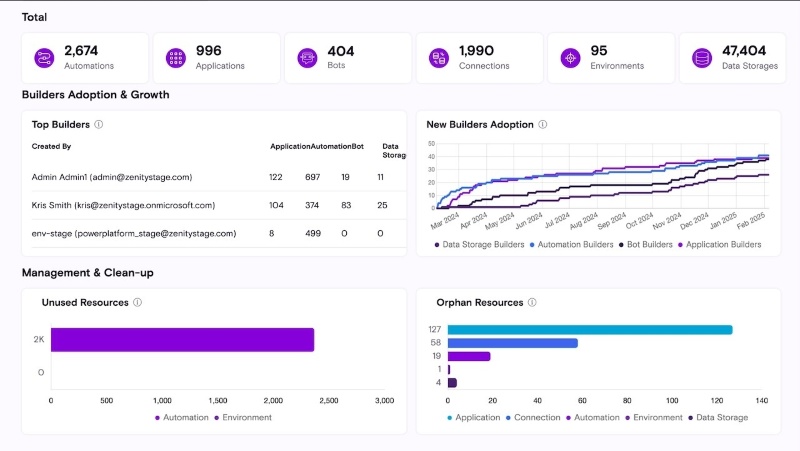
 Suitable For
Suitable For- Enterprises deploying AI agents with tool use and actions
- Teams using Copilot Studio, Foundry, or custom agent platforms
- Security teams that need agent-specific visibility and policy control
 Not Suitable For
Not Suitable For- Organizations only using simple chat interfaces
- Teams seeking classic data governance first

Compare top endpoint management software in 2026, including Intune, Workspace ONE, ManageEngine, Ivanti, and AnySecura, for secure device management and DLP. Learn more>>
7. Microsoft Purview DSPM for AI
If your organization is already using Microsoft 365—and especially if you are beginning to roll out Copilot—Microsoft Purview DSPM for AI is your go-to choice. In such environments, data is already centralized in systems like SharePoint, OneDrive, and Teams, and the essence of AI usage is simply "calling upon that existing data."
Its biggest strength is ecosystem leverage. If your data already lives in Microsoft 365, SharePoint, OneDrive, Teams, and Copilot environments, Purview can use existing data, permissions, and compliance foundations rather than forcing a separate security stack. Microsoft also emphasizes central management, preconfigured reports, and policies, which lowers adoption friction for large enterprises standardizing around Microsoft.
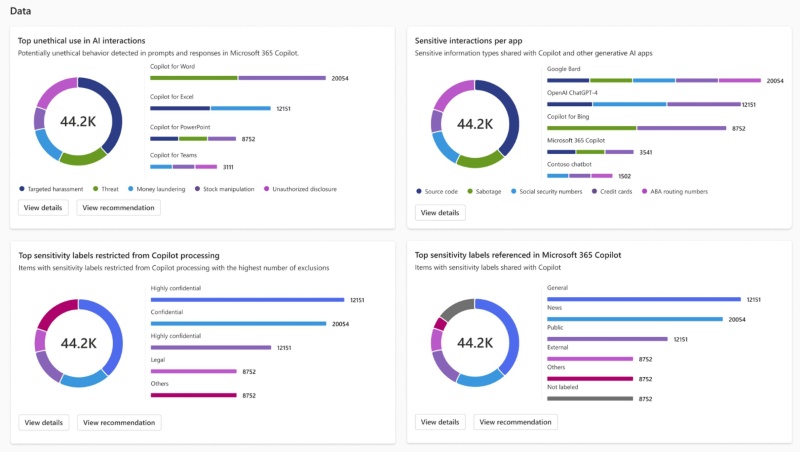
However, it is an extension that is highly dependent on the Microsoft ecosystem. Once your data is no longer within the Microsoft ecosystem—or is distributed across multiple platforms, its advantages diminish accordingly.
 Suitable For
Suitable For- Microsoft-first enterprises (already deep in M365 + Copilot)
- Organizations with mature data governance already in place
 Not Suitable For
Not Suitable For- Multi-platform / non-Microsoft environments
- Teams looking for "AI threat protection" (model-level security)
- Organizations expecting strong enforcement / blocking
8. Lakera Guard
Lakera Guard is built to protect LLM applications at the interaction layer. Its core job is to inspect prompts and responses for risks such as prompt injection, jailbreaks, data leakage, and other unsafe behavior before those issues turn into an application-level incident. That makes it most relevant for teams shipping chatbots, copilots, assistants, and agent-like experiences, especially when they connect LLMs to internal tools or sensitive data.
Lakera has built its name around prompt injection research and production guardrails, which is exactly where many first-wave enterprise GenAI deployments feel the most pain. For organizations that need a specialized control in front of LLM calls, Lakera is easier to understand and often faster to justify than a broader AI security platform. Lakera also points to real enterprise use, including Dropbox’s public reference to using Lakera Guard for LLM-powered applications.
Lakera is not the product you buy to secure model artifacts, govern your full AI inventory, or manage broad AI compliance programs. If your main problem is model supply chain risk, AI discovery, or lifecycle-wide governance, Lakera will usually need to sit alongside other tools rather than replace them.
 Suitable For
Suitable For- Enterprises deploying customer-facing or employee-facing LLM apps
- Teams worried about prompt injection and unsafe model interactions
- Security teams that want a focused control in front of GenAI workflows
 Not Suitable For
Not Suitable For- Organizations mainly concerned with model file scanning
- Companies looking for a full AI governance platform
- Firms that have little or no LLM application footprint
9. Robust Intelligence AI Firewall
Robust Intelligence is useful if you need a policy layer in front of AI applications. You typically need this when your LLM is exposed to users or connected to internal data, where every prompt and response becomes a potential risk. It inspects interactions in real time to block prompt injection, data leakage, and unsafe outputs before they turn into incidents.
Since the company is now part of Cisco AI Defense, it also fits more naturally into broader enterprise security stacks.
The AI firewall category became prominent largely because Robust Intelligence helped define it early, and Cisco’s integration gives the technology stronger enterprise reach than a standalone startup might have on its own. For buyers that want runtime guardrails plus a bigger enterprise security story behind them, that combination is appealing.
The limitation is overlap and ecosystem fit. If you already have a prompt-injection specialist, or if your need is broader governance or model artifact security, the AI firewall alone may not be enough. Also, now that the vendor story is tied more closely to Cisco AI Defense, some buyers may prefer the larger Cisco framing while others may see that as less AI-native than before.
 Suitable For
Suitable For- Enterprises deploying high-risk GenAI apps
- Cisco-aligned security environments
 Not Suitable For
Not Suitable For- Teams focused mainly on model supply chain
- Organizations looking for AI governance as the main need
How to Choose Right AI Security Solutions for Your Team
1. If your main risk is employee AI usage
If employees are using ChatGPT, Copilot, or other AI tools in browsers, IDEs, or SaaS platforms, your biggest problem is data exposure through prompts and outputs.
- If your environment is tool-diverse with shadow AI usage → choose AnySecura
- If your environment is Microsoft-centric (M365, Copilot, Teams) → go with Purview DSPM for AI
2. If you are building LLM applications
If your team is developing chatbots, copilots, or AI-powered workflows, your main risk is prompt injection, unsafe outputs, and uncontrolled model behavior.
- Need fast, lightweight runtime protection → Lakera Guard
- Need policy enforcement, validation, and testing before deployment → Robust Intelligence
3. If you operate your own ML models
If your organization trains or hosts models, the risk shifts to model-level threats—including adversarial inputs, model extraction, and supply chain risks.
- Need runtime detection and monitoring of model attacks → HiddenLayer
- Need model scanning and supply chain security → Protect AI Guardian
4. If your biggest gap is visibility and governance
If your organization lacks visibility into how AI is being used, your main risk is uncontrolled AI adoption, unknown data exposure, and lack of governance across teams.
- Need enterprise-wide visibility, risk posture assessment, and compliance reporting → Cranium
- Need to control and secure AI agents (especially within SaaS environments like Copilot) → Zenity
5. If you want to proactively test AI risks
If your organization already has AI systems in production and a mature workflow, the next step is continuous security testing.
- Mindgard
FAQs about AI Security Solutions
Why are AI systems vulnerable to security threats?
AI systems rely on large datasets, exposed APIs, and complex pipelines. These components create new attack surfaces where attackers may steal models, manipulate inputs, or extract sensitive data.
What is the difference between AI security software and traditional cybersecurity tools?
Traditional cybersecurity tools focus on networks and systems. AI security software focuses specifically on protecting AI pipelines, datasets, models, and AI APIs.

Learn what SentinelOne is, its key features, pros and cons, pricing, and how it compares to other endpoint security solutions. Learn more>>
Conclusion
Organizations that deploy AI systems without proper security controls may expose sensitive data or valuable intellectual property. By adopting integrated AI security platforms and strong governance practices, enterprises can protect their AI systems while continuing to innovate.
If you're concerned about employees misusing AI tools and unintentionally exposing sensitive company data—and want to avoid incidents like the Meta data leak—solutions like AnySecura can help you monitor, control, and protect how AI is used across your organization.


