Recently, the Google Threat Intelligence Group (GTIG) published its 2025 Global Zero-Day Exploitation Trends Report, providing a comprehensive analysis of how zero-day vulnerabilities were exploited in real-world attacks over the past year.
The report makes one thing clear: zero-day exploitation is no longer a rare occurrence. Instead, it has become a persistent part of today’s cybersecurity landscape.
Enterprise infrastructure is now the primary target of many attacks, while artificial intelligence is accelerating both offensive and defensive cybersecurity capabilities. At the same time, the threat ecosystem is expanding. Commercial surveillance vendors, nation-state groups, and financially motivated attackers are all actively exploiting zero-day vulnerabilities.
As unknown threats continue to grow, traditional security approaches based primarily on patching and signature detection are struggling to keep up. Organizations increasingly need proactive, behavior-driven security strategies to reduce the risks posed by modern zero-day attacks. Additionally, enterprise infrastructure remains the main target for attackers.
Zero-Day Vulnerabilities in 2025: High Numbers and Record Enterprise Targeting
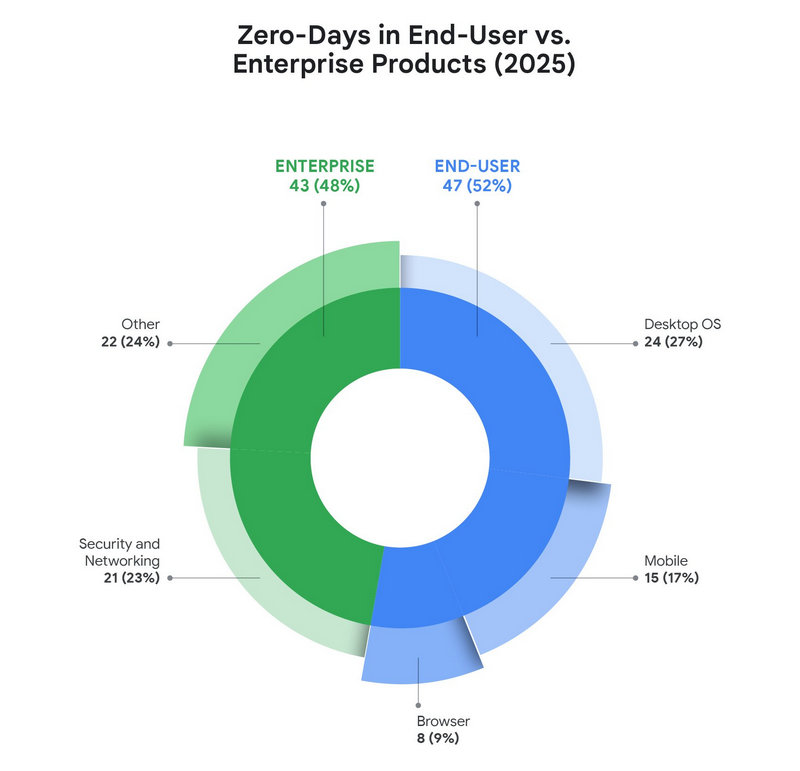
According to GTIG, 90 zero-day vulnerabilities were actively exploited in the wild in 2025.
While slightly lower than the 2023 peak of 100 vulnerabilities, the number still exceeds the 78 reported in 2024. For four consecutive years, the total has remained between 60 and 100, indicating that zero-day exploitation has become a sustained and normalized threat rather than an occasional event.
The report highlights several important trends shaping today’s threat landscape:
- 48% of exploited zero-day vulnerabilities targeted enterprise technologies. A total of 43 vulnerabilities affected enterprise products, marking the highest number and percentage ever recorded.
- Edge devices, security appliances, and networking equipment have become preferred entry points for nation-state espionage groups. More than half of targeted attacks began with vulnerabilities in these systems.
- Operating system vulnerabilities surged, accounting for 44% of all zero-day exploits and becoming the most common attack vector.
- Browser-based exploits dropped to a historical low. However, the report notes that this may not necessarily indicate fewer attacks, but could also reflect improved attacker stealth and operational security.
- Commercial surveillance vendors (CSV) surpassed traditional nation-state actors for the first time, becoming the largest users of zero-day vulnerabilities and lowering the barrier for sophisticated attacks.
- Financially motivated cybercriminal groups are also increasing their use of zero-days. Nine vulnerabilities were linked to ransomware operations or data-theft campaigns, posing direct financial risks to enterprises.
Together, these findings highlight a major shift in the threat landscape. Enterprises are no longer indirect victims of advanced attacks — they are now the primary targets.
In many cases, a single unpatched vulnerability or poorly protected endpoint can provide attackers with the initial foothold needed to compromise an entire corporate network.
Threat Outlook for 2026: AI Will Reshape Cybersecurity
The report also predicts that artificial intelligence will significantly reshape the cyber threat landscape in 2026, introducing several major changes.
AI Will Accelerate the Attack Lifecycle
Attackers are increasingly using AI to:
- automate vulnerability discovery
- generate exploit code more efficiently
- perform large-scale reconnaissance
This automation significantly shortens the time-to-exploitation window between discovering a vulnerability and launching attacks, making it much harder for defenders to respond quickly enough.
The Goal Is Shifting From “Stealing Data” to “Stealing Capabilities”
GTIG also notes a growing trend where attackers compromise technology companies in order to steal:
- source code
- development documentation
- proprietary technologies
These materials allow attackers to independently research and develop new vulnerabilities. Over time, this creates a cycle of:
intrusion → intellectual property theft → vulnerability research → new attacks
Expanding Attack Surfaces Increase Enterprise Risk
Modern enterprises rely on more applications, devices, remote endpoints, and cloud services than ever before. While this improves productivity and flexibility, it also dramatically expands the attack surface.
Attackers only need a single weak entry point to bypass traditional security boundaries and move laterally across the network.
In this environment of unknown vulnerabilities and rapidly evolving threats, traditional defenses based solely on patch updates and signature detection are no longer sufficient.
Organizations must move toward proactive security models focused on endpoint protection, behavior monitoring, and strong data safeguards.
Defending Against Zero-Day Attacks: What Enterprises Should Do
According to the GTIG report, effective zero-day defense requires a strategy built around proactive detection and rapid response.
Key Principles
- enforcing least-privilege access
- reducing the overall attack surface
- strengthening behavioral monitoring
- blocking lateral movement inside the network
- implementing strong data protection and audit visibility
Enterprise-Level Security Practices
Organizations should focus on strengthening infrastructure security by:
- isolating edge devices and critical assets
- closing unnecessary network ports
- removing unused software and services
At the same time, companies should improve anomaly detection by monitoring behavior patterns and establishing baseline activity to identify suspicious changes.
Incident response capabilities are also critical. Maintaining software inventories, enabling rapid system isolation, and preserving detailed logs can help security teams respond quickly and investigate attacks effectively.
Endpoint-Level Protection
At the endpoint level, organizations should ensure:
- timely patch installation
- strong system security configurations
- cautious handling of unknown links and attachments
- advanced browser security protections
As the report highlights, the goal of zero-day defense is not necessarily to eliminate every vulnerability. Instead, the priority is to prevent attackers from expanding their access or stealing critical data once a vulnerability has been exploited.
AnySecura: A Multi-Layer Defense Against Zero-Day Threats
The trends identified in the report — enterprise-focused attacks, patchless vulnerabilities, multi-path intrusion, and data-theft campaigns — require a more comprehensive security strategy.
AnySecura addresses these challenges by building a security framework centered on endpoint control, behavior monitoring, and data protection, covering the entire attack lifecycle from prevention to detection and response.
Reduce the Attack Surface Through Endpoint Control
AnySecura enables organizations to manage enterprise endpoints with fine-grained control, helping reduce potential attack entry points.
- Network access compliance checks that verify device security before allowing network access
- Peripheral and port control, blocking unauthorized external devices and closing unnecessary network ports
- Software and service management that prevents installation of untrusted applications and disables unused services
These measures significantly reduce opportunities for attackers to exploit zero-day vulnerabilities.
Detect Exploitation Through Behavior Monitoring
Because zero-day vulnerabilities often have no known signatures or patches, behavior monitoring becomes a critical security layer.
AnySecura focuses on detecting suspicious activity once exploitation attempts begin, including:
- abnormal process execution
- memory injection attempts
- privilege escalation activities
It also monitors network behavior to block unauthorized outbound connections, large-scale data transfers, and access to suspicious domains.
Protect Sensitive Data Throughout Its Lifecycle
Many zero-day attacks ultimately aim to steal sensitive corporate information.
AnySecura addresses this risk by providing full lifecycle data protection, including:
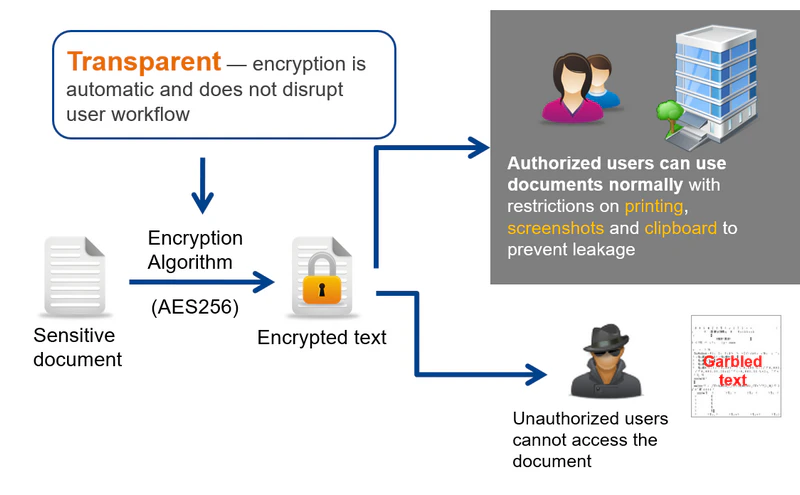
- transparent document encryption to protect sensitive files and source code
- controlled external sharing with permission management and watermarking
- complete auditing of data access and movement
These controls help prevent data loss even if attackers manage to gain access to internal systems.
Rapid Detection and Incident Response
Fast detection and containment are critical when dealing with zero-day attacks.
- tamper-proof operation logs
- real-time security alerts and visual dashboards
- remote isolation of compromised devices and termination of malicious processes
Security policies can also be deployed quickly across multiple endpoints to contain threats.
Prevent Lateral Movement With Least-Privilege Access
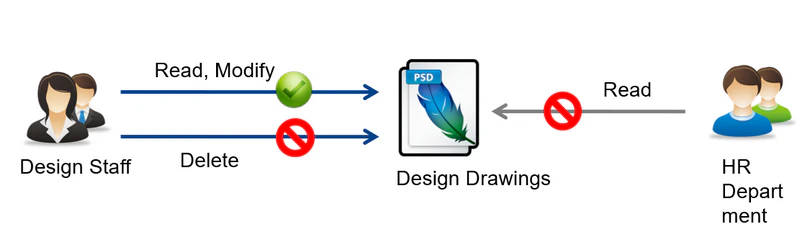
To limit the spread of attacks inside the network, AnySecura enforces strict access control policies, including:
- role-based user permissions
- multi-factor authentication for sensitive assets
- network and data isolation between departments
These controls help ensure that even if attackers gain an initial foothold, they cannot easily expand their access across the organization.
Conclusion
As zero-day vulnerabilities become increasingly common, organizations can no longer rely solely on patching and traditional detection methods.
By combining attack surface reduction, behavioral monitoring, data protection, audit traceability, and strict access control, AnySecura provides a comprehensive security framework designed to defend against modern cyber threats.
This proactive approach prepares enterprises not only for today’s zero-day risks but also for the AI-driven threat landscape of the future — ensuring attackers cannot easily enter systems, steal sensitive data, modify critical assets, evade detection, or escape investigation.