Is your company struggling with employees spending excessive time on social media or streaming sites during work hours? Are you concerned about unusual network activity that could affect productivity or even put sensitive data at risk? Watching how people use the internet at work fixes those problems but you must stay within the law. A clumsy approach angers employees plus brings court cases.
Learning the exact statutes that apply to your location is a basic before boosting efficiency. In this guide, we’ll provide an 8-step actionable plan based on the legal framework in your country, helping you to Monitor Employee Internet Usage Legally and Effectively.

What Is Employee Internet Usage Monitoring?
Employee internet usage monitoring is the continuous observation, recording, and analysis of how staff use the internet on company-owned devices. This process tracks visited websites, bandwidth usage, files uploaded or downloaded, web applications launched, and any activity that could expose the company to risk or violate policies.
The table below is here to help you understand the key metrics to watch when monitoring internet usage and what each one can tell you about your company’s network activity.
| Category | What Is Typically Monitored |
|---|---|
| Web Access |
◦ Websites and domains accessed
◦ Website categories (e.g., social media, entertainment, malicious sites) ◦ Time, frequency, and duration of access ◦ Records of blocked or policy-triggered website access attempts |
| Network Traffic |
◦ Upstream and downstream bandwidth usage
◦ Types of network traffic and protocols (e.g., HTTP/HTTPS, FTP) ◦ High-volume or anomalous traffic patterns ◦ Traffic spikes that may affect business system performance |
| Downloads / Uploads |
◦ Download and upload event logs
◦ File types (e.g., ZIP, EXE, PDF, CAD files) ◦ File size and transfer direction ◦ Use of external cloud services, file-sharing platforms |
| Web Apps / Cloud Services |
◦ Access to SaaS and web-based applications
◦ Use of unauthorized or high-risk cloud services (Shadow IT) ◦ Frequency of use and active time periods ◦ Data synchronization or external sharing activities |
| Online Collaboration |
◦ Access to web-based instant messaging tools
◦ Use of online meeting and collaboration platforms ◦ Network connection records generated by communication tools |
| Security / Compliance Signals |
◦ Attempts to access known malicious or phishing websites
◦ Indicators of communication with malware or command-and-control (C2) infrastructure ◦ Access attempts that violate corporate network or security policies ◦ Anomalous or high-risk behavioral patterns |
| Behavioral Patterns |
◦ Differences between work-hour and non-work-hour internet usage
◦ Access patterns inconsistent with job roles or responsibilities ◦ Long-term trend analysis rather than single-event judgment |
| Audit-Ready Logs |
◦ Access logs (time, source, destination)
◦ Security or policy-triggered event records ◦ Policy enforcement and response outcomes ◦ Administrative access and operation audit trails |
Is Monitoring Employee Internet Usage Legal?
In most jurisdictions, monitoring employee internet usage is legal if it is done transparently, proportionately, and for legitimate business purposes. Problems arise when monitoring is excessive, secretive, or disconnected from a clearly defined need.
To make this clearer, it helps to look at how different regions regulate employee internet usage monitoring in practice.
European Union
| Employee Monitoring Policy Requirement | Compliance Expectation |
|---|---|
| Governing law / regulatory framework | General Data Protection Regulation (GDPR) |
| Employee notice obligation | Mandatory (GDPR Art. 13/14) |
| Lawful basis for processing | Must be explicit (legitimate interests / legal obligation) |
| Whether employee consent is valid | Usually invalid (power imbalance) |
| Purpose limitation | Strict |
| Proportionality principle | Core requirement |
| Whether blanket/continuous monitoring is allowed | Generally not allowed |
| Whether covert monitoring is allowed | Rare exceptions (DPIA required) |
| Content-level monitoring (viewing specific webpages/content) | High risk; requires strong justification |
| Data minimization requirement | Mandatory |
| Data retention time limits | Must be limited |
| Access control | Mandatory |
| Additional procedural requirements | DPIA / union or works council |
Although enforcement intensity varies by jurisdiction, regulators consistently communicate the same core expectations for employee internet usage monitoring. Across different regions, their shared requirements can be summarized as follows:
- Document the purpose: Monitoring must be tied to a clearly documented business purpose.
- Minimize scope: Data collection should be limited to the least intrusive level required.
- Be transparent: Employees must be informed in advance.
- Control access: Monitoring data should be restricted to authorized roles.
- Set retention limits: Data must be retained only for defined periods.
8 Steps to Monitor Employee Internet Usage Effectively
1. Define Monitoring Scope and Purpose
Select a lawful ground for the data gathering, typically “legitimate interest” or a statutory mandate, plus confine the effort to company owned gear. Collect only the types of web traffic required to satisfy the aim. Guard proportionality: do not sweep private material indiscriminately. Put the rationale in a written statement so every reader sees that checks serve explicit business ends.
2. Establish a Clear Monitoring Policy
Draft or revise an Internet Use besides Monitoring Policy that states what will be watched and why, names the people who will handle the logs but also spells out how records will be used or stored. Place the policy in a staff handbook or equivalent notice. Staff must encounter it first hand to ensure openness. Use plain terms to list allowed and forbidden online conduct, e.g. “Employees may not stream video, except for work needs” as well as set out compliance steps plus sanctions for misuse.
3. Select and Configure Monitoring Tools
Choose a monitoring solution that lets you enforce your policy without excess.
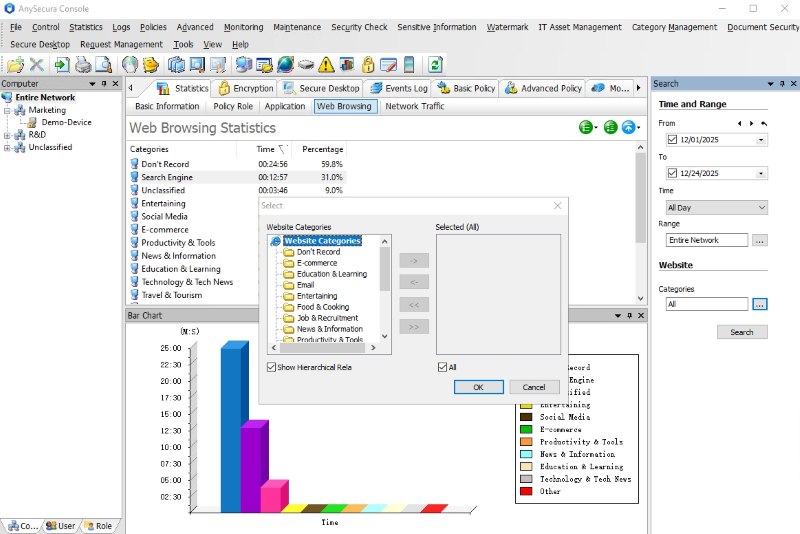
AnySecura provides an extensive set of features to help IT teams monitor usage effectively. It allows you to monitor only the modules you need. Its granular policy controls let you configure monitoring to capture just the data types relevant to your defined scope, nothing more. Once you determine your monitoring boundaries, you can selectively enable activity capture, giving you control and precision from the start while ensuring compliance and flexibility.
With AnySecura, you get access to a wide range of features, such as:
Web Activity Monitoring
- Full Web Logging: Track all websites visited with detailed logs, including full URL, timestamp, and user identity.
- Per-User Activity Logs: Search and review browsing history of specific employees for investigation or audit purposes.
- Real-Time Monitoring: View live user screens and current web sessions for high-risk roles or on-demand checks.
- Website Categorization: Automatically group visited websites into categories like social media, news, shopping, or entertainment.
- Application Usage Tracking: Monitor how much time employees spend in specific desktop or web applications, with departmental rollups.
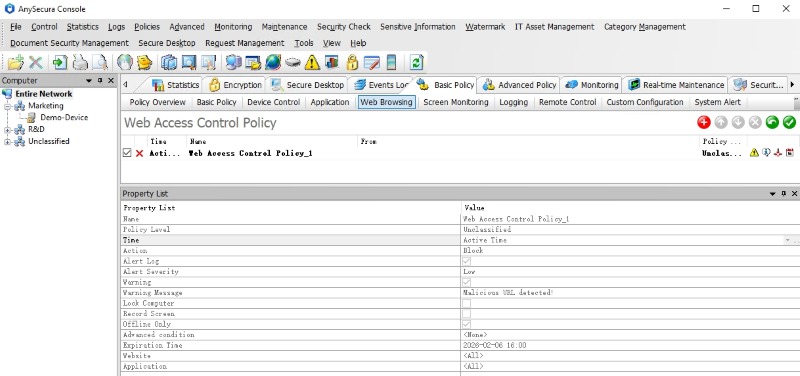
Access Control & Enforcement
- Category-Based Access Rules: Block non-business categories such as gaming, adult, or entertainment by role, team, or schedule.
- User- or Department-Specific Blocking: Apply tailored blocklists (e.g., disabling YouTube for call center staff but not marketing).
- Policy-Driven Blocking Modes: Define enforcement levels such as alert-only, warning pop-up, soft block, or full deny.
- Custom Filter Lists: Create custom allow/deny rules at the domain or category level to align with business needs.
- Bandwidth Throttling / Traffic Caps: Limit how much bandwidth specific users or groups can consume on non-essential websites (e.g., video streaming).
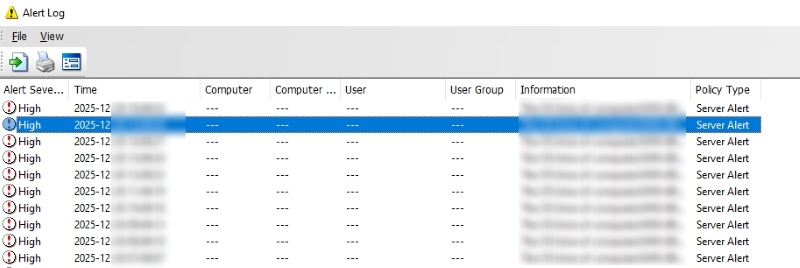
Alerts & Oversight
- Notifications & Rule-Based Alerts: Get real-time alerts when employees access unauthorized, high-risk, or flagged domains.
- Malware & Threat Detection: Scan for malicious URLs or behaviors and alert IT when threats are identified.
- Audit Logging & Role-Based Access: Track who accessed logs or monitoring settings, and control visibility using RBAC.
Usage Analytics & Optimization
- Department-Level Usage Reports: Generate reports showing web and app usage trends across teams or offices.
- Time-Based Access Trends: Analyze when employees are accessing non-essential sites and adjust policies accordingly.
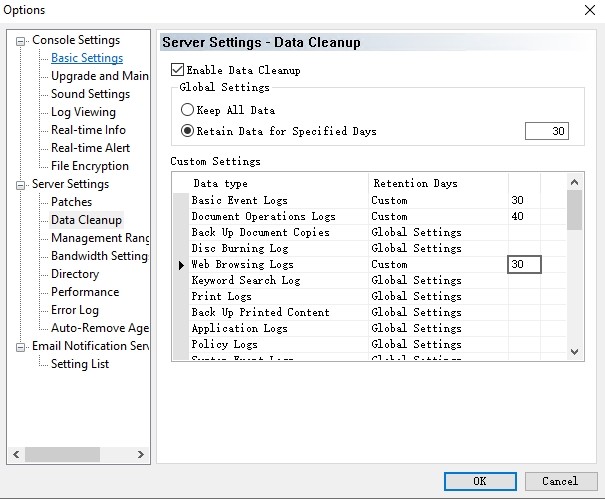
- Retention Settings & Data Minimization: Automatically purge logs based on retention policy (e.g. 60–90 days) to reduce storage and compliance risk.
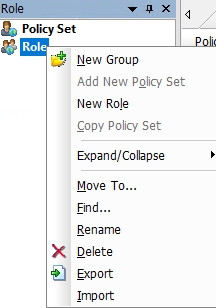
4. Implement Role-Based Access Controls
Limit the people who read or edit monitoring data. Assign the right to open logs only to named administrators, security staff or compliance officers. Build a role based scheme: HR staff receive no path to raw browser logs, IT teams receive no right to change security rules. Record every attempt to reach the monitoring console or its data. The record must show who viewed or exported which item. Firm internal rules stop misuse and allow inspection only when a valid reason exists.
5. Communicate with Employees
Maintain openness. Inform staff in advance that monitoring will occur, many laws plus standards demand it. Publish the new or revised policy through email, training sessions or the intranet. State plainly which web actions will be recorded and state the reason, like protecting systems or enforcing acceptable use. Stress that the goal is to guard the firm but also help productivity, not to pry into private messages.Each worker must know what to expect. Involving employees raises trust as well as lends fairness to the program.
6. Set Data Retention and Minimization Rules
Store only what you need. Define a clear retention period for each type of log (e.g. keep web logs for 60–90 days, then delete). Configure your monitoring tool to automatically purge old records according to that schedule. Avoid collecting irrelevant personal data, focus on URLs and usage stats, not the contents of unrelated communications. Keep all monitoring data securely (encrypted or on a protected server) and regularly clean up expired logs.
7. Review and Adjust Regularly
Monitoring needs change over time, so audit your approach periodically. Verify that the data collected is still necessary and being used only as intended. Tweak rules if needed, for example, loosen restrictions if overblocking, or tighten them if risks rise. Conduct occasional privacy impact checks (DPIAs) especially if adding new monitoring (like screenshot capture). Keep the scope and intensity proportional: don't expand monitoring without a new justification.
8. Document and Audit Compliance
Maintain records to show you're following the rules. Keep an internal log of your monitoring activities (often called a Record of Processing Activities) and track changes to policies or configurations. If you rely on consent or legitimate interest, note how that was determined. Log any access to monitoring data and any incidents. Provide training to admins so they handle the data responsibly. Having clear documentation and audits ready shows regulators or auditors that you respect transparency, purpose limitation, and data protection, demonstrating that your monitoring is both effective and compliant.

A simple guide on how to monitor employees working from home, including productivity tracking, basic rules, and how to avoid invading privacy.Learn more>>
Benefits of Monitoring Employers Internet Usage
Organizations benefit from tracking internet activity because it helps protect the business and its data. With workers accessing cloud services, mailboxes, and collaboration hubs daily, monitoring ensures sensitive information stays secure, whether leaving the company intentionally or accidentally. By following the steps outlined above, you’ll also gain the benefits listed below.
Enhanced cybersecurity is another key benefit. By keeping an eye on traffic, organizations can spot risky behavior early, block access to dangerous sites, phishing links, and unsafe downloads, and prevent malware or ransomware from spreading.
Regulatory compliance is made easier. Industries that handle personal data, financial records, or intellectual property can demonstrate that they safeguard sensitive material, with internet usage logs providing an audit trail and evidence of effective controls.
Monitoring improves productivity and resourcanyse management. Insights from internet activity reveal patterns of heavy personal browsing, streaming, or use of unauthorized tools, helping managers set clearer policies or provide targeted training, rather than relying on guesswork or micromanagement.

Learn what compliance monitoring is, how it works, and how businesses use tools to meet regulations and reduce risk.Learn more>>
FAQs about How to Monitor Employee Internet Usage
Do we need to inform employees before monitoring their internet usage?
Yes. In most jurisdictions, transparency is a legal and ethical requirement. Employees should be informed through policies, onboarding materials, or written notices explaining what is monitored, why, and how the data is used.
Can we monitor all internet activity, including private emails or messages?
Generally not. Monitoring must be proportionate to the stated business purpose. Content-level surveillance (such as reading messages) should only occur with clear justification, and never for purely personal communication unless there is a policy violation or legal obligation.
What kind of data should we collect and what should we avoid?
Collect only what is necessary: URLs, timestamps, device/user IDs, and category types are typically sufficient. Avoid collecting passwords, personal account info, or detailed content unless explicitly justified.
Conclusion
Monitoring employee internet usage doesn't have to be invasive or complex, when done right, it protects both your company's operations and your employees' trust. By following clear steps rooted in purpose, transparency, and proportionality, IT teams can implement a responsible monitoring strategy that meets business and compliance goals.
AnySecura gives you the tools to monitor smarter, with full control over what's captured, who can access it, and how it aligns with your policies.


