Maybe you’re a small business owner or entrepreneur who’s heard that “compliance monitoring is important” but has no idea where to start—and the thought of all those technical terms makes your head spin. Or maybe you’re an IT manager putting together employee policies, data usage rules, or security processes, looking for practical tips and tools that actually work.
Either way, you’re in the right place. In this article, we’ll break down what compliance monitoring really is, why it matters, and how to do it right, so you can strengthen your company’s management, keep data safe, and reduce risks without getting overwhelmed.

What Is Compliance Monitoring?
Compliance monitoring refers to the process of reviewing and evaluating whether an organization complies with rules, usually ongoing. These rules can come from government authorities, industry bodies, contractual obligations, or the company’s own compliance policies. When it is ignored, companies can run into damages from legal trouble to ruined trust.
What Is Being Monitored in Compliance Monitoring?
These rules usually come from three main sources:
1. Laws and Regulations (External Rules)
These are legal requirements set by governments and regulators. Examples include:
- Data protection laws like GDPR or HIPAA
- Financial regulations such as anti-money laundering (AML) rules
- Industry standards like PCI-DSS for payment security
Compliance monitoring checks whether daily business actions follow these legal obligations.
2. Internal Company Policies (Internal Rules)
Every organization sets its own standards, such as:
- Acceptable use policies for company devices
- Data access and sharing rules
- Security and confidentiality guidelines
Monitoring ensures employees follow these policies, even when no external law is directly involved.
3. Contracts and Business Commitments
Some rules come from agreements with clients or partners, for example:
- Promises to protect customer data
- Reporting obligations in service contracts
Compliance monitoring helps verify that these commitments are being honored.

Learn how to monitor employee internet usage legally and ethically and best practices.Learn more>>
What is Not Compliance Monitoring?
In companies, monitoring can focus on many different areas and answer very different questions. You may think some types of monitoring are part of compliance monitoring, but they are not. Here is a table to help you distinguish.
| Type of Monitoring | Main Question It Answers | Primary Focus |
|---|---|---|
| Performance Monitoring | Are employees working efficiently? | Productivity, speed, output |
| System Monitoring | Are IT systems running properly? | Uptime, errors, system health |
| Security Monitoring | Is there a cyber threat or attack? | Hacking, malware, breaches |
| Compliance Monitoring | Are we breaking any rules? | Laws, regulations, policies |
Why Compliance Monitoring Is Important?
Compliance monitoring matters because the legal and financial consequences of failure can be severe. The cases below illustrate the significant impact of neglecting compliance monitoring across different industries.
Preventing fraud and strengthening stability
Failing to watch transactions closely brings harsh penalties, danske Bank missed money laundering clues and moved more than two hundred billion dollars of suspect funds, the bank received record fines plus its name still suffers. Because of such losses, banks now treat strong anti-money-laundering programs that watch activity second by second as a core shield against fraud.
Building trust as well as dodging fines
Hospitals and insurers must follow tight privacy rules, HIPAA in the United States, GDPR in Europe, to guard patient records.
Anthem lost control of data for roughly seventy nine million people in 2015, the firm later paid sixteen million dollars under HIPAA or a further one hundred and fifteen million to settle a class action suit. Those events prove that weak oversight of who sees patient files triggers massive costs next to tarnishes reputations.
Ensuring safety and raising quality
Manufacturers answer to many workplace safety, product standard but also environmental protection rules. OSHA and the EPA issue directives every plant must obey. Monitoring compliance here includes checking guards on machines, logging each drum of hazardous waste, verifying that every worker finished required training as well as comparable steps. Meeting those duties wards off fines and injuries and, in many plants, lifts product quality.

What Is a malicious insider? Learn how to identify different types, spot warning signs, and use effective strategies to protect your organization’s data and systems.Learn more>>
How to Monitor Compliance with the Right Tools
1. Know the rules you must obey
Every trade imposes its own set of laws and benchmarks, turn the duty into practical steps
- Link each statute to an inside activity: Decide which clause touches which unit, privacy law on the IT crew, money handling rules on accounts, safety codes on the shop floor.
- Draft a rule-by-rule roster: Split every statute into verifiable tasks, encode secret files, record cash approvals, weigh poison trash before it leaves the gate.
- Name a single steward: DGive one person or squad final say for each slice of the law so oversight never drifts.
2. Establish an Internal Compliance Monitoring System
Once requirements are clear, companies can design a system to track and analyze compliance effectively:
- Define what to audit: List specific activities and records to monitor, such as database access logs, transaction approvals, equipment inspection reports, employee training completion, or environmental sensor data.
- Set audit frequency and thresholds: Determine how often reviews should occur and define what triggers a warning or alert, for example repeated unauthorized access or failed safety checks.
- Analyze patterns and trends: Look beyond individual incidents and identify recurring violations, risk spikes, or unusual behavior across teams or systems.
- Document corrective actions: Record each issue, investigation, and resolution step to maintain audit readiness and continuous improvement.
3. Choose the Right Solutions and Tools
Compliance monitoring often involves many moving parts, but using the right software makes it more manageable. These solutions offer automation, insights, and better control over your organization’s policies.
- Government, Risk, and Compliance (GRC) Platforms: Track incidents, manage risks, and improve overall compliance oversight.
- Compliance Management Systems (CMS): Simplify and standardize compliance workflows across the organization.
- Security Information and Event Management (SIEM): Detect, investigate, and respond to security incidents quickly.
- Data Loss Prevention (DLP) Tools: Monitor and protect sensitive information from unauthorized access or sharing.
- Privacy Management Tools: Help organizations meet data protection and privacy regulations with ease.

Discover how DLP software delivers compliance, prevents insider threats, and secures sensitive information across endpoints, cloud services, and networks.Learn more>>
Using the right tools helps make compliance monitoring easier and more effective by spotting problems early and keeping your organization up to date with regulations.
Building a Reliable Compliance Monitoring System with AnySecura
AnySecura is a comprehensive workforce monitoring and data protection platform designed to help organizations maintain strong compliance standards across daily operations.
Here's how you can use AnySecura to monitor employee compliance and enforce internal policies.
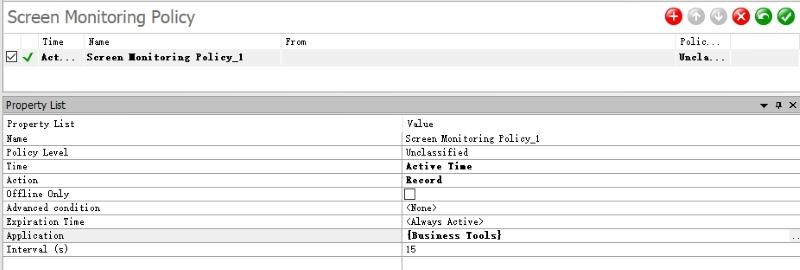
- User Activity Monitoring: Records application usage, website visits, keystrokes, and screen activity so compliance teams can review how employees interact with regulated systems and verify policy adherence.
- Audit Logs: Automatically creates time-stamped records of user actions and system access, providing audit-ready evidence for internal reviews and regulatory inspections.

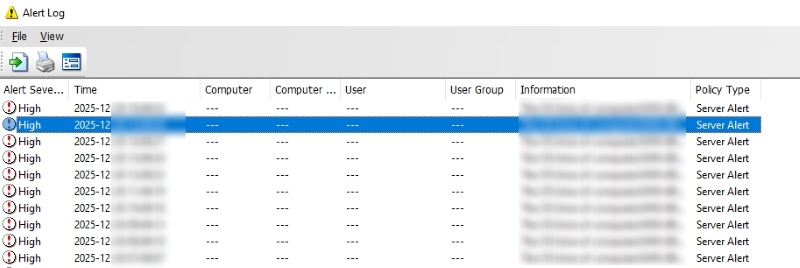
- Real-Time Alerts: Triggers notifications when predefined rules are violated (e.g., access to sensitive data after hours or unauthorized file sharing), allowing teams to respond to compliance risks immediately.
- Data Loss Prevention (DLP): Detects and blocks attempts to transfer sensitive data outside approved channels, helping organizations comply with data protection and privacy regulations.
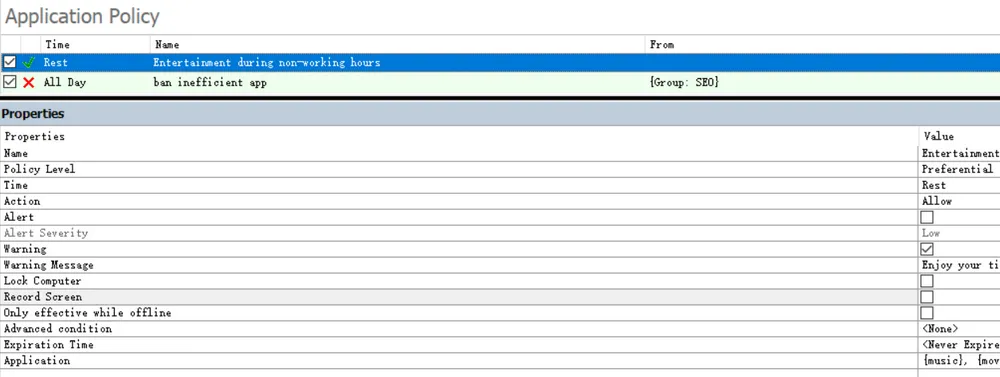
- Policy Enforcement Rules: Allows organizations to define and enforce compliance policies through automated controls, ensuring consistent application across departments.
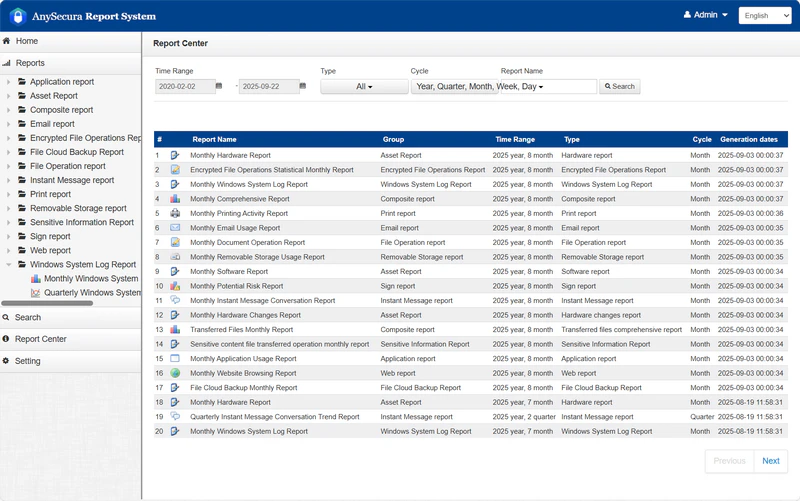
- Report Generation: Produces structured compliance and activity reports that can be shared with auditors, regulators, or internal stakeholders.
- Access Control Integration: Links user activity to roles and permissions, helping verify that employees only access systems and data they are authorized to use.
FAQs about Compliance Monitoring
Can compliance monitoring impact employee privacy?
It will if the firm hoovers up more information than it needs. Publish plain rules, gather only the data required for proof and lock that data behind narrow doors, the checks will still catch breaches without trampling on people or statutes.
Who is responsible for compliance monitoring?
Typically, the compliance team, risk management officers, IT security teams, and sometimes internal audit departments share responsibility.
Conclusion
Compliance monitoring guard the firm, keep it within the law and stop faults before they spread. Clear instructions, sound tools but also frequent reviews let the business run without nasty surprises.
Want to see how it works? Try AnySecura demo today and check out real-time monitoring and easy reporting.


