How to Configure Encryption Permissions in Document Security Management with AnySecura | User Guide
This guide will help you master the encryption permissions within AnySecura's Document Security Management module. You'll learn how to define what users and computers can do with encrypted files, from requesting decryption to securely exporting documents.
We'll then explore how to build a flexible and manageable policy structure. You'll understand how to apply settings across different groups and leverage inheritance to create consistent yet granular controls over your organization's sensitive data.
Encryption permission settings define the permissions for clients with encryption authorization when connected to the server. Permissions can be configured for Windows, Mac, and Linux clients.
| Icon Button | Description |
|---|---|
 |
Edit — encryption permissions for the selected computer or user |
 |
Delete — encryption permissions for the selected computer or user |
 |
Export — policy file, import policy file, or copy the current policy to other clients |
Encryption can be configured for computers and domain users. If a computer or user has custom permissions, a small red flag appears at the top-right corner of its icon.
Administrators can set encryption permissions at multiple levels: entire network, computer groups → computers, user groups → users, and policy collections. Permission priority (from highest to lowest) is:
User Policy > User Role Policy > User Group Policy > User Group Role Policy > Computer Policy > Computer Role Policy > Computer Group Policy > Computer Group Role Policy
Lower-priority policies act as parent group policies for higher-priority ones. For example, for a computer policy, all lower-priority policies—including computer role, computer group, and computer group role policies—serve as its parent group policies.
When setting encryption permissions, General, Authorized Software, and Secure Zone can be configured to inherit parent group policies:
- If inheritance is disabled, only the object's own policies apply.
- If inheritance is enabled, the object's policies are combined with parent policies. Inheritance continues up the hierarchy if parent groups also have inheritance enabled; it stops if a parent group disables inheritance, inheriting only that level's policy.
- Inheritance is independent for General, Authorized Software, and Secure Zone settings.
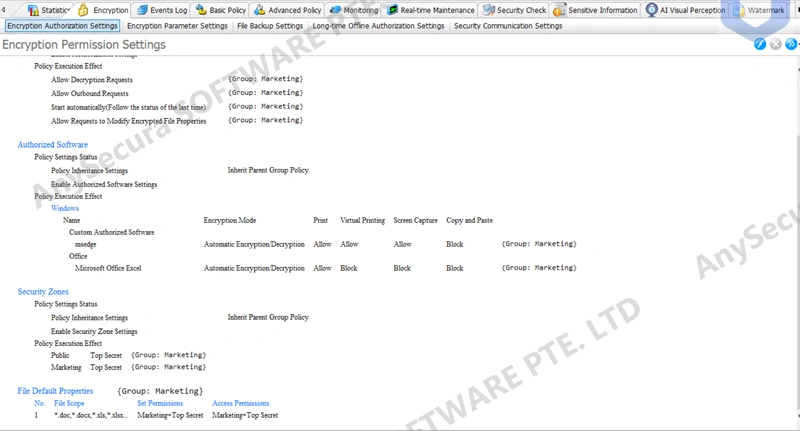
After configuring encryption policies, administrators can preview the policy effect for a selected object. In the preview, General, Authorized Software, and Secure Zone are displayed in two sections: policy settings and policy execution effect. The execution effect shows the object's final combined policy and the source of each policy.
General
| General Permissions | Description |
|---|---|
| Policy Inheritance | Dropdown to select Do Not Inherit Parent Policy or Inherit Parent Policy. New policies default to Inherit Parent Policy + Authorization Disabled. Inheriting parent policies combines policies across objects; not inheriting applies only the object's own policy. |
| Enable Authorization Settings | When checked, settings below (e.g., allow decryption requests) become active. |
| Allow Decryption Requests | Default encryption permission; users can request document decryption from administrators. |
| Advanced Settings | Restrict which files can be requested for decryption by clients. |
| File Name | Defaults to all files. Specific file types (e.g., *.dwg, *.dxf) can be set, with separate inclusion and exclusion lists; exclusions take precedence over inclusions. |
| Security Properties | Defaults to all attributes and levels. Specific secure objects and levels can be set with inclusion and exclusion ranges; exclusions take precedence. |
| Allow Direct Decryption | Permission to decrypt encrypted files directly without administrator approval. |
| Advanced Settings | Limits the number or total size of files that clients can decrypt directly. Enable Settings must be checked for the following options to take effect. |
| Time | Cycle for quota calculation; choose Daily or Hourly. |
| Quantity Quota | When checked, set the maximum number of files that can be decrypted within the cycle. |
| Size Quota | When checked, set the maximum total file size (in MB) that can be decrypted within the cycle. |
| Action | Determines behavior when quota is exceeded: Deny prevents further decryption; Allow permits continued decryption. |
| Alarm | When checked, exceeding the quota triggers an alert in the console; alert levels can be adjusted. |
| Warning | When checked, set a warning message to display on the client when the quota is exceeded. |
| Backup Decrypted Documents | Back up decrypted files; the backup is the original encrypted file before decryption. |
| Backup Range | Only documents within this size range will be backed up. |
| Allow Outbound Requests | Users can request external release of documents from the administrator. |
| Advanced Settings | When requesting external release, restrict the selectable external release objects and configuration; external release configuration can be chosen from existing templates via the  button or set manually. Click the button or set manually. Click the  button to save the current settings as a new external release template. button to save the current settings as a new external release template. |
| Outbound Recipients | When a client requests file export, it can only be sent to designated recipients. It can also be configured to require at least one recipient for each export request. |
| File Configuration | When a client requests file export, each permission can only be set as specified. Printing, Virtual Printing, Clipboard, Screenshot, Editing, Auto-Delete, Hide:
|
| Allow Direct Outbound | Generate exported documents directly without administrator approval. |
| Advanced Settings | Restrict recipient selection and export configuration when the client exports files directly. See Advanced Settings for Export Request Permissions for details; settings are similar. |
| Backup Outbound Files | Backup exported documents. |
| Backup Range | Only exported documents within this size range will be backed up. |
| Allow Extraction of Authorized Outbound Files | Clients can extract exported documents with access rights within their own permissions. |
| Allow Extraction of Higher-Privilege Outbound Files | Clients can extract exported documents with access rights higher than their own. |
| Allow Request to Modify Encrypted Document Properties | Clients can request administrators to modify encrypted document properties. |
| Additional Advanced Settings | When set for domain users or groups, further advanced options can be configured per user. When clients request document property changes, restrictions can be applied to searchable/viewable audiences and user permissions. |
| Reading Audience | Settings below take effect only when "Enable User Permission Control" is checked;
|
| User Permissions | When the client modifies document user permissions, each file permission can only be set as specified.
|
| Template Settings | When modifying document user permissions, the client can only select from templates set by the administrator.
|
| Allow Direct Modification of Encrypted Document Properties | Modify encrypted document properties directly without administrator approval. |
| Advanced Settings | When setting for domain users or groups, additional per-user advanced options can be configured. When the client directly modifies encrypted document properties, restrictions apply to searchable or browsable audiences and user permissions. See Advanced Settings for Modification Request Permissions for details; the settings are similar. |
| Allow Proxy Admin Login | Allows administrator accounts to log in as a proxy admin on the client for decryption and export approvals. |
| Allow Client to Logout of Encryption System | The client can log out of the encryption system while online. All encryption functions are disabled upon logout and restored after logging back in. |
| Encryption Login Method | If Allow Client to Logout of Encryption System is checked, the client can log out of the encryption system.
|
When the "Inherit Parent Group Policy" option is selected, the client policy is combined with the parent group policy. The combination rules are as follows:
- 1.Checked-Type Settings (e.g., "Allow Decryption Request", "Allow Direct Decryption"): If any combined policy has the option checked, the final effect is Checked.
- 2.Advanced Settings (e.g., "Advanced Settings" for "Allow Decryption Request" or "Allow Export Request"): The final effect follows the highest-priority policy based on policy matching.
- 3.Backup Range Settings (e.g., "Backup Range" for "Backup Decrypted Documents" or "Backup Exported Documents"): The final effect follows the highest-priority policy based on policy matching.
- 4.Encryption Function Activation Method: Priority is as follows: Force Manual Login > Force Automatic Login > Automatic Login (retain previous state) > Allow Client to Set. The highest-priority setting present in the combined policies becomes the final effect.
Note:
- For Linux and Mac clients, only "Allow Decryption Request" and "Allow Direct Decryption" take effect when configuring general encryption permissions. Other settings are currently not supported.
Authorized Software
For transparent encryption, authorized software must be selected manually. For read-only encryption, when a client opens an encrypted document in read-only mode, the software used automatically becomes the authorized software.
| Authorized Software Permission | Description |
|---|---|
| Policy Inheritance | Dropdown to choose Do Not Inherit Parent Policy or Inherit Parent Policy. New policies default to Inherit Parent Policy + Disable Authorized Software Settings. Inherited policies combine across objects; non-inherited policies apply only to the object itself. |
| Enable Authorized Software Settings | Check to activate the authorized software settings below. |
| Name | Name of the authorized software. Settings can be configured under the Windows, Linux, or Mac tabs. |
| Encryption Mode | Four modes are available for authorized software:
|
Additionally, you can configure whether printing, virtual printing, screenshots, and clipboard usage are allowed for each authorized software. This setting applies to both transparent encryption and read-only encryption.
If Inherit Parent Group Policy is selected, the client policy is combined with the parent policy. The combination rules are:
- 1. Enable Authorized Software: If any combined policy enables the software, the final effect is Enabled.
- 2. Authorized Software Permissions: The final effect follows the settings in the highest-priority policy based on policy matching.
Note:
- 1. For Linux clients, only Automatic Encryption/Decryption and Decrypt-Only take effect when setting the authorized software encryption mode. Other modes are treated as Automatic Encryption/Decryption.
- 2. For read-only encryption, if the program used to open an encrypted file is not set as authorized software, printing, virtual printing, screenshots, and clipboard operations are all prohibited.
Security Zone
Specifies the security zones and levels of documents that a client can open. For example, a client with Marketing Confidential permission can open documents at the Marketing Confidential level or lower, but cannot access any documents in the Finance department.
| Security Zone Permission | Description |
|---|---|
| Policy Inheritance | Dropdown to choose Do Not Inherit Parent Policy or Inherit Parent Policy. New policies default to Inherit Parent Policy + Disable Security Zone Settings. Inherited policies combine across objects; non-inherited policies apply only to the object itself. |
| Enable Security Zone Settings | Check to activate the security zone settings below |
When Inherit Parent Group Policy is selected, the client policy is combined with the parent policy. The combination rules are:
- 1. Security Zones and Levels: Priority is as follows: All Zones & Levels > All Zones with Specified Levels > Specified Zones & Corresponding Levels. The highest-priority setting determines the final effect.
- 2. Within the Same Zone: Security level priority is Top Secret > Confidential > Secret > Internal > General. The highest-priority level takes effect.
Default Document Properties
By default, encrypted documents are set to Public Zone – General Level with no user permissions. You can configure all documents or specific documents with designated security zones, levels, and user permissions.
| Options | Description |
|---|---|
| Set Default Properties for New Encrypted Documents | Check to activate the settings below |
| File Scope |
|
| Document Properties |
|
| User Permission Control |
Settings below take effect only when Enable User Permission Control is checked. |
Note:
- This setting applies only to newly created encrypted files. Existing encrypted files will not have their security properties changed.
